Blog
How Chinese-Nexus Cyber Operations Have Evolved – And What It Means For Cyber Risk and Resilience
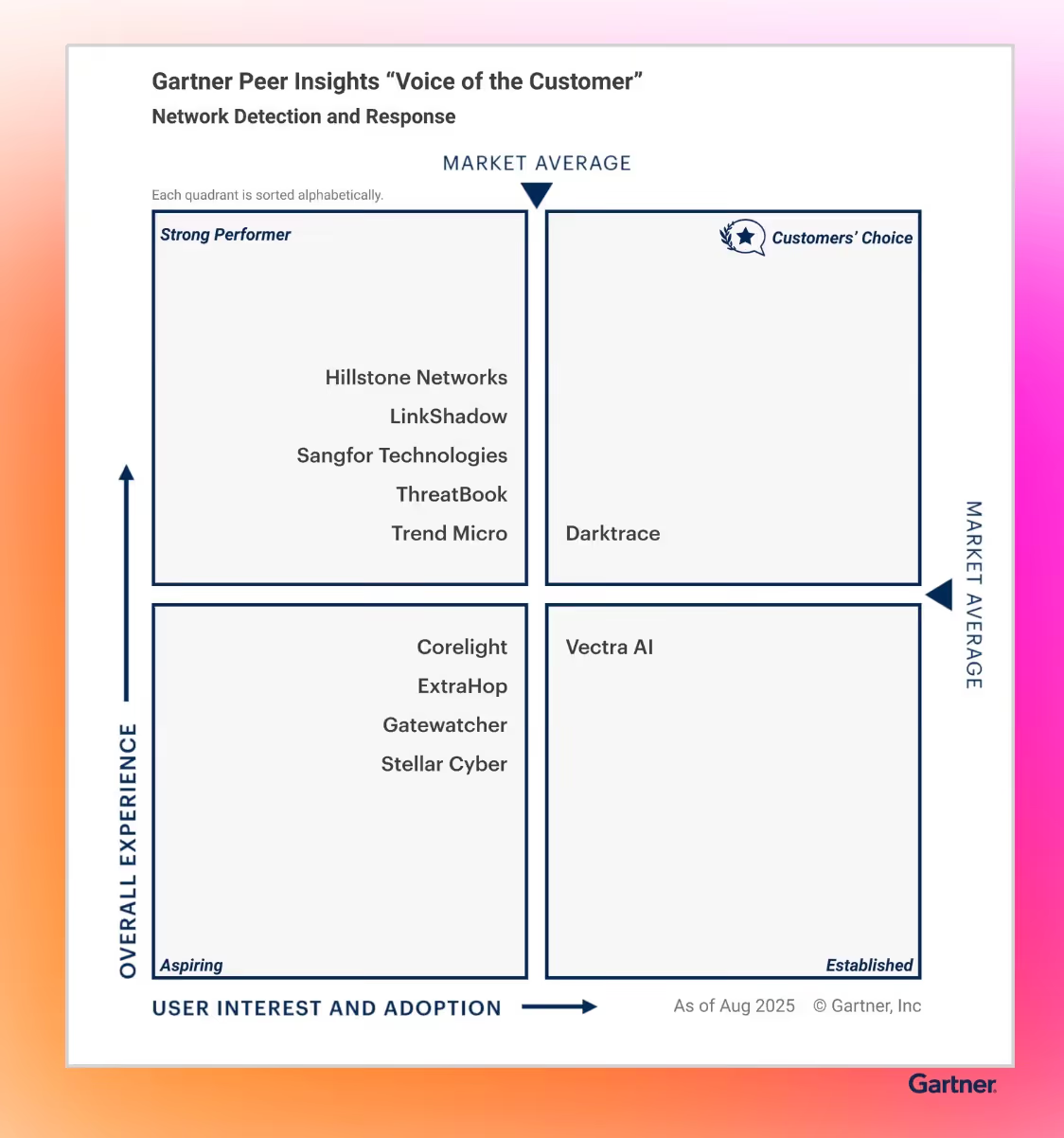
Darktrace's latest threat research reveals how Chinese-nexus cyber operations have evolved from isolated intrusions into long-term strategic positioning, with attackers prioritizing persistent access to critical infrastructure and digital ecosystems to gain lasting operational and economic advantage.