Cryptocurrencies are hitting the headlines every week and quickly becoming accepted as a mainstream investment and method of payment. Across the world, cyber-criminals are leveraging data centers called crypto-mining ‘farms’ to profit from this trend, from China to Iceland, Iran, and even a cardboard box in an empty warehouse.
How does cryptocurrency mining work?
Cryptocurrencies are decentralized digital currencies. Unlike traditional currencies, which can be issued at any time by central banks, cryptocurrency is not controlled by any centralized authority. Instead, it relies on a blockchain, which functions as a digital ledger of transactions, organized and maintained by a peer-to-peer network.
Miners create and secure cryptocurrency by solving cryptographic algorithms. Rather than hammers and chisels, crypto-miners use specialized computers with GPUs or ASICs to validate transactions as quickly as possible, earning cryptocurrency in the process.
Crypto-mining farms in 2021: Reaping the early harvest
Crypto-mining takes up an enormous amount of energy. An analysis by the University of Cambridge estimates that generating Bitcoin consumes as much, if not more, energy than entire countries. For instance, Bitcoin uses approximately 137.9 terawatt hours per year, compared to Ukraine, which uses only 128.8 in the same period. Bitcoin is just one of many cryptocurrencies, alongside Monero and Dogecoin, so the total energy consumed by all cryptocurrencies is far higher.
Given that high-powered mining computers require so much processing power, crypto-mining is lucrative in countries with relatively cheap electricity. However, the energy needed can lead to serious consequences – even shutting down entire cities. In Iran, the outdated energy grid has struggled to provide for cryptocurrency farms, resulting in city-wide blackouts.
While some of these crypto-farms are legal, illegal crypto-miners are also straining Iran’s energy supplies. Illegal crypto-mining is popular in Iran partly because Iranian currency is volatile and subject to inflation, whereas cryptocurrency is (for the moment) immune to both inflationary monetary policy and U.S. sanctions. When used for illegal purposes, cryptocurrency farming can lead to network outages and serious financial harm.
Crypto-mining malware in corporate networks
Crypto-mining malware has the ability to hamper and even crash an organization’s digital environment, if unstopped. Cyber AI has discovered and thwarted hundreds of attacks where devices are infected with crypto-mining malware, including:
- a server in charge of opening and closing a biometric door;
- a spectrometer, a medical IoT device which uses wavelengths of light to analyze materials;
- 12 servers hidden under the floorboards of an Italian bank.
In one instance last year, Darktrace detected anomalous crypto-mining activity on a corporate system. Upon investigation, the organization in question traced the anomalous activity to one of their warehouses, where they found what appeared to be unassuming cardboard boxes sitting on a shelf. Opening these boxes revealed a cryptocurrency farm in disguise, running off the company’s network power.

Figure 1: The unassuming cardboard boxes

Figure 2: The cryptocurrency farm
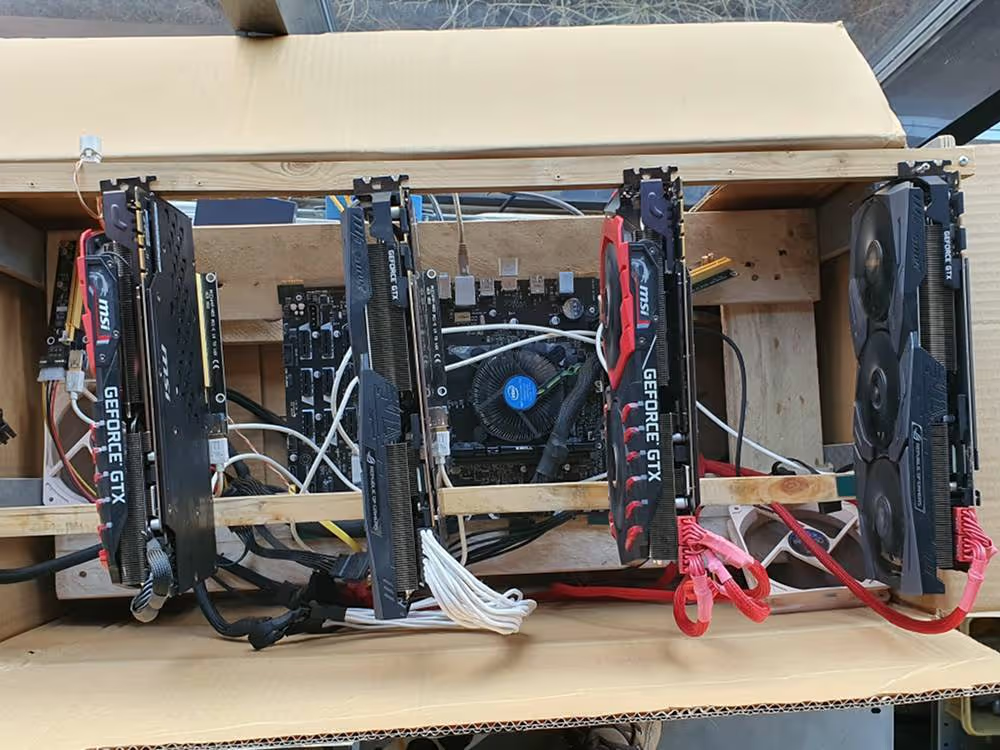
Figure 3: The threat actors created a stealthy cryptocurrency mining rig with GPUs, running off the company’s network power
Had it remained undiscovered, the crypto-mining farm would have led to financial losses for the client and disruption to business workings. Mining rigs also generate a lot of heat and could have easily caused a fire in the warehouse.
This case demonstrates the covert methods opportunistic individuals may take to hijack corporate infrastructure with crypto-mining malware, as well as the need for a security tool which covers the entire digital estate and detects any new or unusual events. Darktrace’s machine learning flagged the connections being made from the warehouse boxes as highly anomalous, leading to this unexpected discovery.
In organizations with Darktrace RESPOND active, any anomalous crypto-mining devices would be blocked from communicating with the relevant external endpoints, effectively inhibiting mining activity. RESPOND can also enforce the normal ‘pattern of life’ across the digital environment, preventing malicious behavior while allowing normal business activities to continue. As bad actors continue to proliferate and hackers devise new ways to deploy crypto-mining malware, Darktrace’s full visibility and Autonomous Response in every part of the digital environment is more important than ever.
Thanks to Darktrace analyst Chloe Phillips for her insights.
Darktrace model detections:
- Compliance / Crypto Currency Mining Activity
- Compromise / High Priority Crypto Currency Mining
- Compromise / Monero Mining
- Anomalous Connection / Rare External SSL Self-Signed
- Compromise / HTTP Beaconing to Rare Destination
- Compromise / POS and Beacon to Rare External
- Compromise / Slow Beaconing Activity to External Rare
- Compromise / SSL Beaconing to Rare Destination
- Compromise / Sustained TCP Beaconing Activity to Rare Endpoint
- Anomalous Connection / Multiple Failed Connections to Rare Destination
- Compromise / Sustained SSL or HTTP Increase
- Anomalous Connection / Connection to New TCP Port
- Anomalous Connection / Connection to New UDP Port
- Compromise / Multiple UDP Connections to Rare External Hosts
- Compromise / SSL or HTTP Beacon
- Compromise / Quick and Regular HTTP Beaconing
- Device / Suspicious domains
- Compromise / Suspicious Beacons to Rare PHP Endpoint
- Anomalous File / Script from Rare
- Anomalous Connection / New failed External Windows Connection
- Device / New Failed External Connection
- Anomalous Connection / POST to PHP on New External Host





































