The FBI estimates that, on average, more than 4,000 ransomware attacks have occurred every day since 2016. Operating at machine speeds, ransomware is capable of wreaking havoc on a digital enterprise within mere seconds. And unfortunately, traditional security tools are only programmed to detect known cyber-threats using rules and signatures – leaving them blind to tailored and novel ransomware threats that have never been seen before in the wild.
Because Darktrace’s fundamental approach to cyber defense does not rely on rules and signatures to identify emerging threats, it is in a unique position to neutralize novel attacks. In one recent customer environment, Darktrace RESPOND (formerly known as 'Antigena') stopped a previously-unknown ‘zero-day’ ransomware attack targeting an electronics manufacturer. Even when deployed over a fraction of the digital estate, Darktrace RESPOND was able to neutralize this never-before-seen ransomware strain before it could do any damage.
Imperfect visibility, perfect response
While Darktrace provides 100% coverage of the entire digital infrastructure, from email and cloud to IoT and networks, business challenges sometimes prevent users from obtaining full visibility into their environment. However, even when working with imperfect data and suboptimal coverage, Cyber AI can still identify ongoing threats as they emerge. In the below attack, Darktrace was not covering the initial stages of the attack lifecycle, including the initial infection and command & control establishment – yet the AI was able to autonomously respond within seconds, before the attack escalated into a crisis.
Anatomy of a ransomware attack
In this example, Darktrace’s AI identified patient zero deviating significantly from its typical pattern of internal behavior. This was illustrated by a spike in the pattern of regular connections made by patient zero and a series of high-confidence alerts firing in quick succession. These included:
- Compromise / Ransomware / Suspicious SMB Activity — triggers when a device begins making unusual SMB connections across the organization
- Antigena Ransomware Block — triggers Antigena to take an action when the behavior is significantly similar to ransomware
- Device / Reverse DNS Sweep — triggers when a device makes unusual reverse DNS lookups, a tactic often used during reconnaissance

Figure 1: Several Darktrace alerts fire, and a deviation from the regular pattern of life is visible
Indeed, not only was the device observed making an unexpectedly large number of connections, but it was also reading and writing a large number of SMB files and transferring this data internally to a server it did not usually communicate with. The spike in internal connections between patient zero and the server was a strong indicator of malware attempting to move laterally through the network.
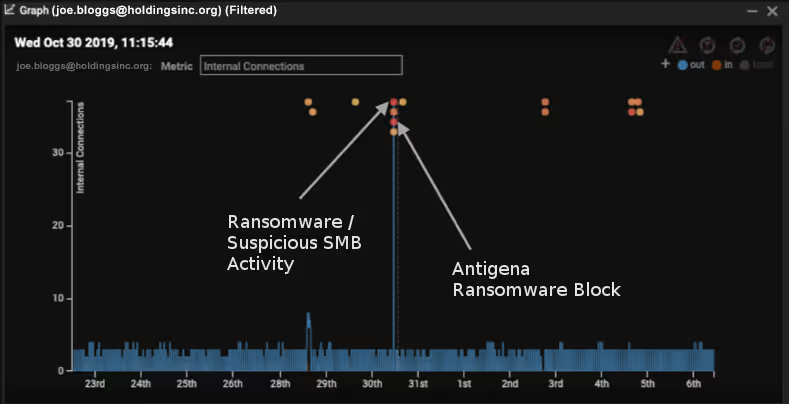
Figure 2: Four model breaches observed on October 30th and a dotted line representing Antigena’s actions
Further investigation into the SMB activity revealed that hundreds of Dropbox-related files were accessed on SMB shares that the device had not previously accessed. Moreover, several of these files started becoming encrypted, appended with a [HELP_DECRYPT] extension.

Figure 3: Darktrace detects SMB activity relating to Dropbox files
Fortunately, Darktrace RESPOND was in Active Mode, and kicked in a second later, enforcing the usual pattern of life by blocking anomalous connections for five minutes, immediately stopping the encryption. By the time Darktrace’s AI took action, only four of these files were successfully encrypted.
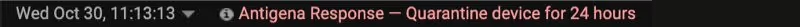
Figure 4: Darktrace RESPOND kicks in 1 second after ransomware was detected
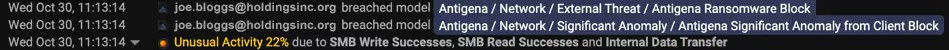
Figure 5: More Antigena (RESPOND) alerts and a clear indication of the unusual activity detected
RESPOND then took a second action to stop the ransomware from spreading to other devices. The combination of various anomalous activities was sufficient evidence for Autonomous Response to neutralize the threat: patient zero was quarantined for 24 hours, unable to connect to the server or any other device on the network.
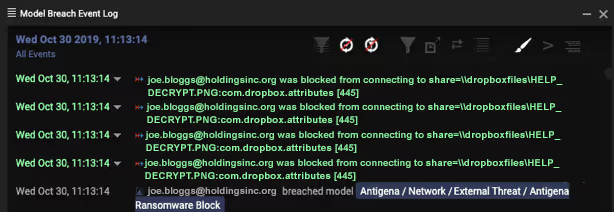
Figure 6: Darktrace stops the infected device from conducting lateral movement & ransom activity
Darktrace RESPOND therefore not only stopped the encryption activity in its tracks, but also prevented the attackers from moving laterally across the network unimpeded – either by scanning, using harvested admin credentials, or performing internal reconnaissance. Autonomous Response initiated a surgical intervention that halted the malware’s spread, all while allowing normal business operations to continue.
No signatures, no problem
Crucially, this strain of ransomware was not associated with any publicly known indicators of compromise such as blacklisted command & control domains or malware file hashes. Darktrace was able to detect this never-before-seen attack based purely on its comprehensive understanding of the normal pattern of life for every device and user within the organization. Once the deviation from this normal behavior was identified, Antigena was able to stop it immediately – without relying on rules, signatures, or historical data. With autonomous response acting decisively and immediately, the security team had enough time to catch up and perform hands-on incident response work.
Darktrace’s AI provides a potent combination: Darktrace DETECT's capacity to reveal deviations in a device’s behavior together with RESPOND acting to block connections and contain the ransomware from spreading across the enterprise. AI-enabled Autonomous Response neutralized the threat by recognizing the lethal recipe of these unusual internal alerts and taking targeted action against the ransomware. This stealthy strain of ransomware is unlikely to have been noticed, let alone stopped, by a security team reliant on legacy tools.
The Return-On-Security-Investment (ROSI) is often discussed when it comes to cyber security expenditure, and this incident provides a great example of the ROSI manifesting itself – recent ransomware attacks usually demand hundreds of thousands of dollars’ worth of ransom payments. Without Darktrace RESPOND containing the threat at an early stage, it is likely that thousands of files would have been encrypted. By relying on Cyber AI, the company was able to take back the advantage over an ever-evolving adversary, saving time, money, resources, and – perhaps most critically – the company’s reputation.



































