For as long as people have sought to protect their assets from intrusion, they have safeguarded those assets behind ever more formidable walls, from castle walls made of stone to firewalls comprised of code. Yet no matter how impenetrable such fortifications appear, motivated attackers will inevitably find a way to bypass them. Build a 50-foot fence, and the enemy will bring a 50-foot ladder. Install state-of-the-art endpoint security on every employee’s computer, and cyber-criminals will infiltrate via the smart refrigerator in the office kitchen.
Needless to say, reinforcing the perimeter is still a good idea. Just as a castle in ruins makes a poor home for a king, so too do weak endpoint defenses put intellectual property and sensitive data at risk. The reality, however, is that digital environments are exponentially more difficult to wall off than physical ones, given the sheer number of applications and users that can compromise an entire network with just a single vulnerability or oversight. Improving a company’s cyber hygiene is therefore a continual responsibility, the nature of which perpetually changes as the business evolves.
Because even flawless cyber hygiene isn’t guaranteed to keep external attackers — let alone malicious insiders — from breaching the perimeter, leading companies and governments have turned to cyber AI technologies. Cyber AI works by learning the particular behaviors of a network and its users, allowing it to pick up on the subtly anomalous activity associated with an already infected device. Such technologies have shined a light on ten of the most commonly exploited cyber hygiene issues, five of which are examined below. And whereas there is no silver bullet when it comes to securing the enterprise online, patching these holes in the perimeter is nevertheless a critical first step.
Issue #1: Using SMBv1 — for anything
Server Message Block (SMB) is a very common application layer protocol that provides shared access to files, printers, and serial ports to devices in a network. The latest version, SMBv3, was developed with security in mind, whereas the original version, SMBv1, is more than three decades old and — in Microsoft’s own words — “was designed for a world that no longer exists[;] a world without malicious actors.” As a result, Microsoft has long implored users to stop using it in the strongest possible terms.
However, many of these users still have not disabled the protocol on operating systems older than Windows 8.1 and Windows Server 2012 R2, which do not allow SMB1 to be removed. The 2017 WannaCry ransomware attack abused the famous exploit EternalBlue in SMBv1 to infect Windows machines and move laterally in Windows environments, precipitating billions of dollars in global losses. Furthermore, SMBv1 allows NTLM logins using the anonymous credential by default, while successful anonymous logins can allow attackers to enumerate the target device for more information.
In light of the serious security risks that SMBv1 introduces, Darktrace flags its usage as threatening with the following models:
- Anomalous Connection / Unusual SMB Version 1 Connectivity
- Compliance / SMB Version 1 Usage
Issue #2: SMB services exposed to the internet
As mentioned above, SMB allows devices in a network to communicate with one another for a variety of purposes — functionalities that render it a complex protocol with many known vulnerabilities. Users are consequently highly discouraged from allowing connections from the internet to internal devices via any version of SMB — not just SMBv1.
Darktrace detected this poor hygiene practice in early 2019, when it observed the use of SMB from external IP addresses connecting to an internal device. The device happened to be a Domain Controller (DC), a server which manages network security and is responsible for user authentication. Due to the critical network function performed by this server, it is a high value target for cyber-criminals, meaning that any external connections should be limited to only essential administrative activity. In this incident, the external device was seen accessing the DC via SMBv1 and performing anonymous login. Fortunately, Darktrace AI detected the potential compromise with the model Compliance / External Windows Communications.
Issue #3: RDP services exposed to the internet
Microsoft’s proprietary Remote Desktop Protocol (RDP) provides a remote connection to a network-connected computer, affording users significant control over another device and its resources. Such extensive capabilities represent the holy grail for attackers, whether they seek to gain an initial foothold in the network, access restricted content, or directly drop malware on the controlled computer. Exposing devices with RDP services to the internet therefore creates a significant vulnerability in the network perimeter, as passwords and user credentials are liable to be brute-forced by those with malign intent.
Last month, Darktrace’s cyber AI detected a large number of incoming connections over the RDP protocol to a customer’s internet-facing device — possible indicators of a brute-force attack. While this activity might have been benign under different circumstances, the AI’s understanding of ‘self’ versus ‘not self’ for the particular device in question enabled it to flag the connections as anomalous, since they breached its Compliance / Incoming RDP from Rare Endpoints model.
By investigating further with Darktrace’s device tracking capability, we can see that the computer also breached several other AI models, including Compliance / Crypto Currency Mining Activity, Compliance / Outbound RDP, and Compromise / Beaconing Activity to External Rare. These breaches suggest that the attackers might have sought to use the computer to plant crypto-mining modules on other network-connected devices.
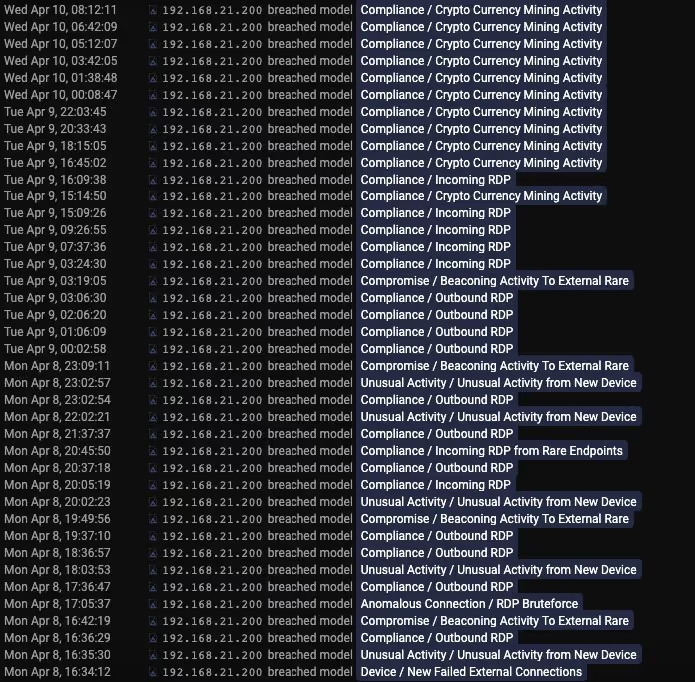
Models that the device breached within three days
Issue #4: Data uploads to unapproved cloud services
No innovation has antiquated the perimeter-only approach to cyber security more than cloud computing, since cloud and hybrid infrastructures have nebulous borders at best. Nevertheless, there are a number of bad cyber hygiene habits that make bypassing perimeter defenses much easier, including employees who upload data to close storage providers that are not on an organization’s approved list. Whether done maliciously or inadvertently, this decision prevents organizations from gaining any visibility over that data being transferred across the globe.
Darktrace cyber AI detects such unauthorized data movements with the following models:
- Anomalous Connection / Data Sent To New External Device
- Unusual Activity / Unusual External Data Transfer
Issue #5: Weak password usage and storage
Among the most common and most avoidable cyber-attacks are those that exploit systems with weak passwords, which can be breached by brute-force or dictionary attacks. Yet stronger, more complex passwords introduce a separate problem: because they are harder to be remember, users tend to store these passwords in sometimes unsafe locations. Whereas passwords housed in encrypted mediums such as password managers are relatively secure, many users instead save them in cleartext. Several modern strains of malware possess the ability to comb through the network in search of possible files which contains passwords, rendering this a critical vulnerability.
Darktrace has a set of models to spot such attempts at password guessing:
- Device / SMB Session Bruteforce
- Unusual Activity / Large Volume of Kerberos Failures
- User / Kerberos Password Bruteforce
- SaaS / Login Bruteforce Attempt
Darktrace also has a set of models that flag anomalous password storage or access:
- Compliance / Sensitive Terms in Unusual SMB Connection
- Compliance / Possible Unencrypted Password Storage
- SaaS / Unusual SaaS Sensitive File Access
Read the second part: Part two — The perils of convenience





































