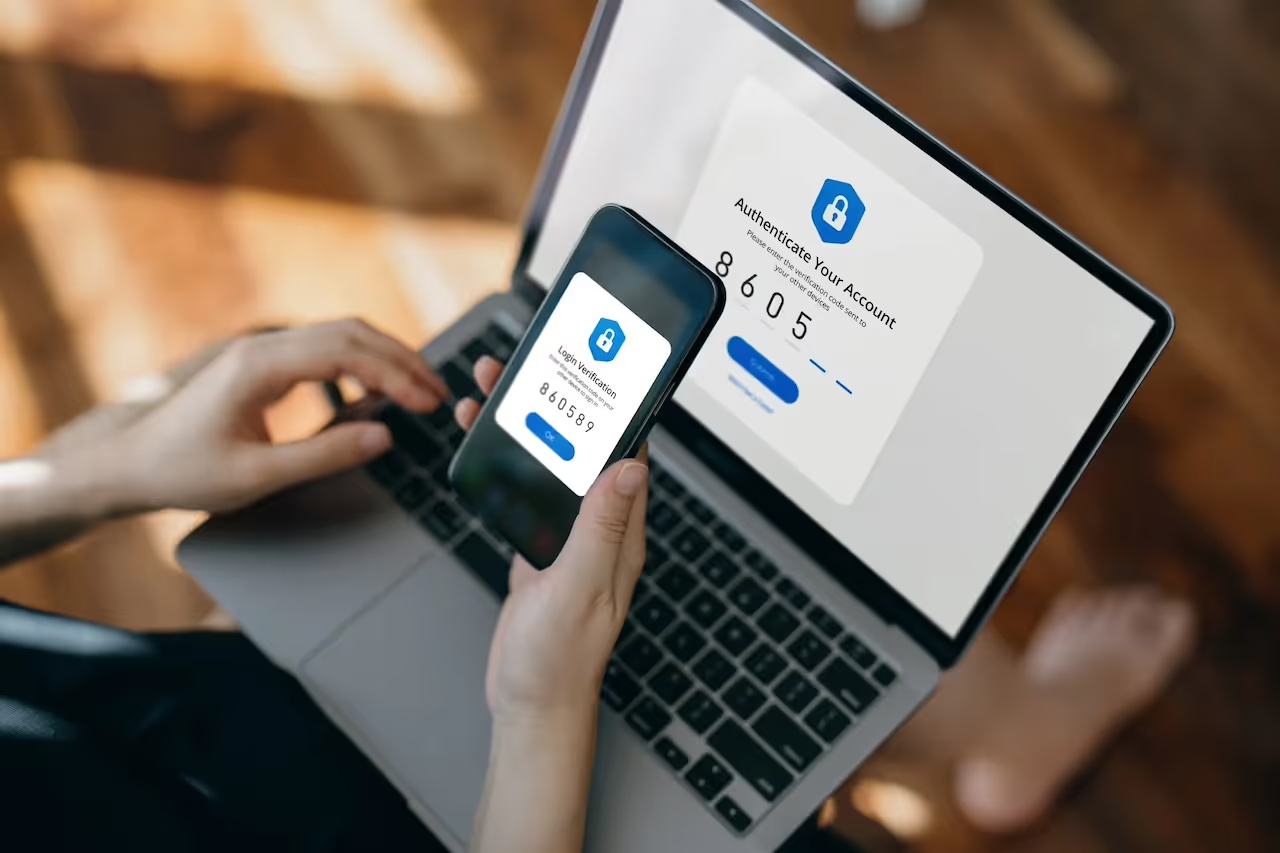
Multi-Factor Authentication (MFA) is a long-established component of the identity and access management (IAM) framework that requires users to provide multiple verification factors to access Software as a Service (SaaS) and application environments, rather than simply relying on account credentials. MFA has been widely, although not universally, adopted as a security measure against common account takeover methods, such as brute-force attacks and exploiting passwords found in data leaks. Despite the adoption of MFA, account takeover methods are still prevalent across the threat landscape. However, the industry is seeing more and more examples of MFA compromise wherein threat actors exploit the security tool itself to gain account access.
Although having a security measure like MFA is a crucial first step in safeguarding a network, relying on a single method will always lead to gaps. MFA is a generic term for a broad range of products and services with varying degrees of efficacy; however, it is often used in the same way as Zero Trust, as a tick box or one size fits all solution. Knowing the gaps in security that are still present, even when utilizing effective MFA tools, is essential to mitigating the evolving threats of account compromise.

Bypassing MFA & Attack Details
Instances of threat actors’ bypassing MFA typically involve an element of social engineering, such as spamming authentication requests to the victim’s email or phone. This takes advantage of the victim’s fatigue of receiving numerous notifications, leading them to validate the request to silence the notifications. Microsoft research data published in September 2022 shows a clear trend of MFA fatigue attacks becoming increasingly popular last year [1]. Notably, the Uber hack occurred after attackers exploited this method [2]. This trend seems likely to continue as MFA progresses towards universal adoption and attackers continue to focus on social engineering as a means to bypass it. The following example details how Darktrace not only identifies and warns customers about unusual MFA activity for hijacked accounts, but also how its suite of products can take appropriate actions to prevent further compromise.
On January 5, 2023, a SaaS account belonging to a customer based in Australia was observed successfully logging in from a rare external endpoint, following two previous failed attempts. Darktrace identified that the login IP address was in the United States, which it recognized as unusual compared to the user’s expected login location, and the successful login followed multiple failed MFA authentication requests.

No further suspicious activity was detected on the device, likely a tactic employed by the threat actor to remain undetected by security tools. However, a Darktrace model breach was triggered two days later following another usual login location, this time in Germany. Once again, a successful authentication request was observed, suggesting the attacker was able to consistently bypass the MFA security and access the account.
Following this login, multiple unusual activities were observed including the access of multiple sensitive internal files and initiating updates to email folders, namely \Sent Items, \Deleted Items, and \WIISE. This type of activity is indicative of a victim’s mailbox being modified to enable attackers to send malicious spam to contacts in the organization, allowing them to escalate their privileges and move laterally throughout the network.

Darktrace continued to report suspicious activity from this user with similar activity occurring again on January 8, when the user was observed logging in from another highly anomalous location and accessing similar files. The activity escalated on January 13 when, alongside an unusual login and further email updates, the user created a new email rule suspiciously named “.”.

The rule appears to have targeted emails received from a specific internal user, marking them as read and moving them to a different folder; it was likely that the attacker intended to use these emails to help socially engineer third-parties and compromise the organization’s network further. Additional suspicious activity was observed from the user, including an update to an email containing a potentially sensitive attachment.

Due to the combination of an unusual login and new email rule, Darktrace RESPOND/Network™ took swift autonomous action, forcing the user in question to log out and disabling the account, preventing further compromise. With the implementation of these actions the malicious actor was unable to engage in any further activity on the compromised account.

Conclusion
Having MFA in place is an important first step towards hardening an organization’s SaaS environment and safeguarding against less sophisticated methods of attack, however defense in depth is key to ensuring a network is truly secure. Any one security measure will always have weaknesses, and only with multiple layers of varying protection can gaps in security be effectively closed.
Using Self-Learning AI™, Darktrace DETECT™ can quickly identify unexpected behavior on a device, even if it occurs with legitimate credentials and successfully passes MFA, to bring it to the attention of the security team. Darktrace RESPOND™ is then able to take immediate action, implementing precise actions to prevent more serious compromise.
Pairing the two products together provides customers with an around-the-clock AI decision maker capable of detecting emerging threats, even those that would evade other traditional security measures, and interrupting attacks at machine speed with surgical precision.