The following guest-authored blog post examines an advanced cyber-threat discovered by Darktrace on a customer’s network.
At Expel — a managed security provider — our analysts get to use a lot of really cool technologies every day, including Darktrace. Given its popularity among our customers, we thought it would be useful to demonstrate how Darktrace helps us identify and triage potential security threats.
Here’s an example of how our team investigated a remote file copy over SMB.
Investigating a Darktrace alert
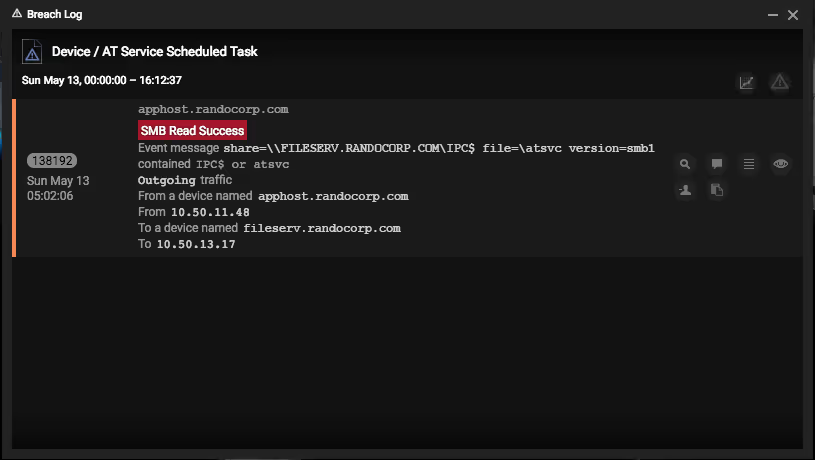
Take a look at this alert. It was triggered via a violation of one of the pre-packaged model breaches for Device / AT Service Scheduled Task.
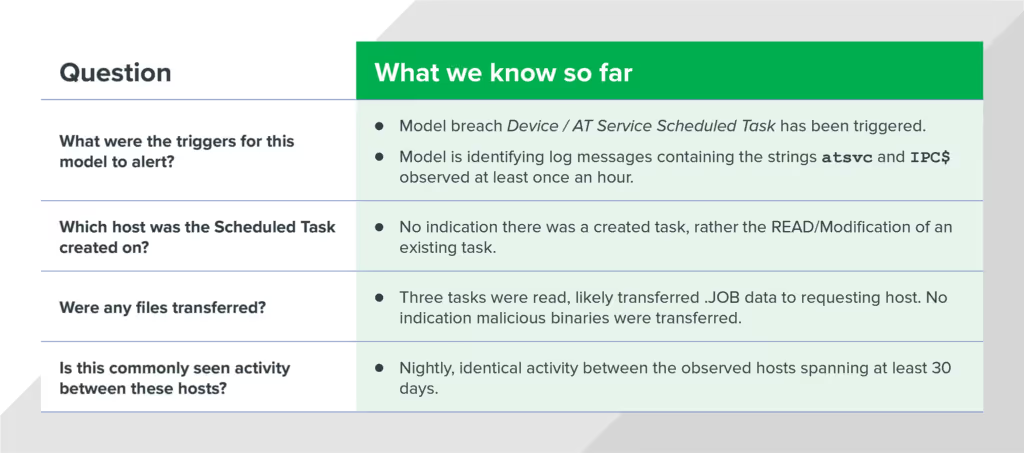
To triage this specific alert, we need to answer the following questions:
- What were the triggers that caused the model to alert?
- Which host was the Scheduled Task created on?
- Were any files transferred?
- Is this activity commonly seen between these hosts?
By answering these questions, we can determine whether or not this alert is related to malicious activity. First, we need to gather additional evidence using the Darktrace console.
At this point, we know the model breach Device / AT Service Scheduled Task was triggered. But what does that mean? Let’s view the model and explore the logic.
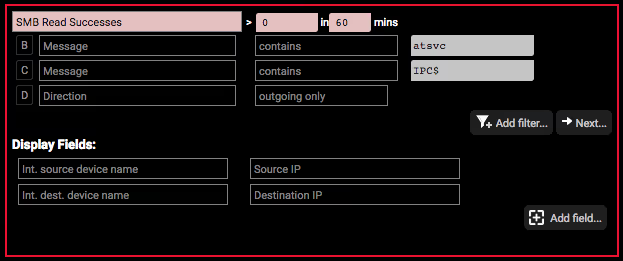
Looking at the logic behind this model breach, we see that any message containing the strings “atsvc” and “IPC$” will match this model breach. And because the frequency has been set to “> 0 in 60 mins,” we can assume that once this activity is seen just one time, it’ll trigger an alert. By understanding this logic, we now know:

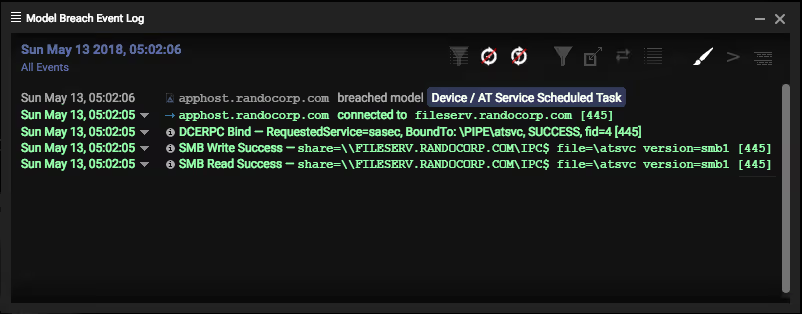
Next, let’s grab some data. We opened the Model Breach Event Log to see the related events observed for this model breach. There was a successful DCE-RPC bind, followed by SMB Write/Read success containing the keywords “atsvc” and “IPC$.”
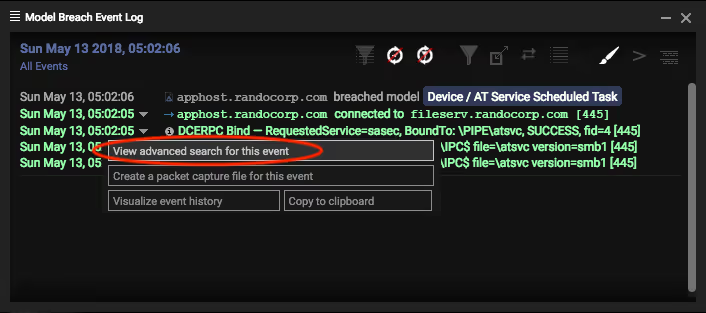
We turned to the View advanced search for this event feature of the Model Breach Event Log for even more info.
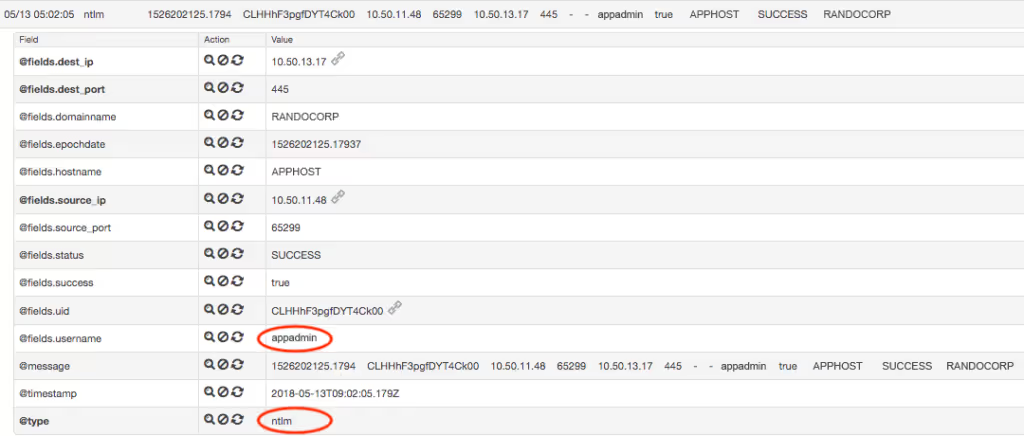
The advanced search results for this model breach revealed two distinct messages. There’s a successful NTLM authentication message for the account “appadmin.” Since NTLM is commonly used with SMB for authentication, this is likely the account being used by the source machine to establish the SMB session.
Immediately after this authentication, we see the following DCE-RPC message for a named pipe being created involving atsvc:

We see that the RPC bind was created referencing the SASec interface. Based on a quick online search, we learned that the SASec interface “only includes methods for manipulating account information, because most SASec-created task configuration is stored in the file system using the .JOB file format0.”
One possible explanation for this connection is that it was made to query information about a scheduled task defined within the .JOB format, rather than a new scheduled task being created on the host. However, Darktrace doesn’t show any messages mentioning a file with the extension “.JOB” within this model breach. So we kept digging for answers.
By querying “*.JOB AND SMB” within the timeframe of the activity we’ve already observed, some promising results appeared:
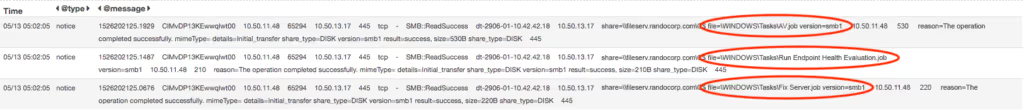
We observed three unique .JOB files being accessed over SMB during the exact time of our previous observations. Considering the hosts and the timeframe, we correlated this activity to the original model breach.
So we know the following:
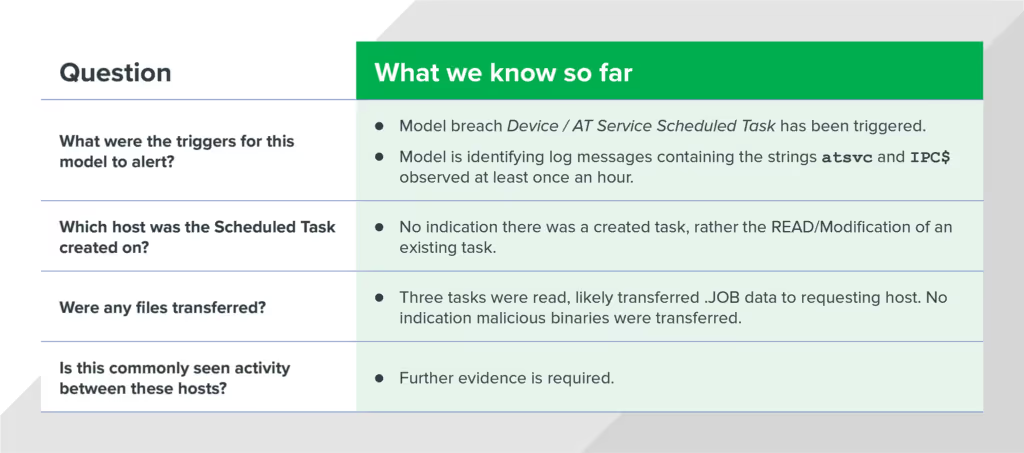
To answer the last investigative question, we used the query “AV.job AND SMB” over the past 60 days. This query returned daily entries for identical activity dating back several months. The activity occurred around the same time each day, involving the same hosts and file paths.

This was starting to smell like legitimate activity, but we still wanted to analyze the contents of the requested file AV.job. We created a packet capture for a five-minute window around the timeframe of the source IP address observed in the model breach.
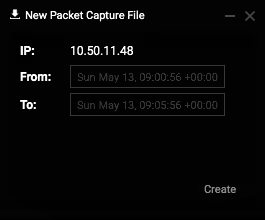
Once we collected the PCAP, we downloaded and analyzed it in Wireshark, and then extracted the transferred files using the Export Objects feature.
The contents of this file refer to an executable in the location C:\Program Files\Sophos\Sophos Anti-Virus\BackgroundScanClient.exe. Judging by the name of the .JOB file this was found in, it was likely a legitimate scheduled task created to perform an antivirus scan on the endpoint each morning.
Reviewing our original analysis questions, we could confidently answer all four questions:
Darktrace’s cyber defense platform allowed our analysts to quickly confirm and scope potential threat activity and identify network-based indicators (NBIs) related to an attack. It can also generate additional, host-based indicators (HBIs) to supplement your investigation. In summary, Darktrace AI enables our Expel analysts quickly and efficiently scope an incident or hunt for threats across the entire organization — without the need for exhaustive data collection and offline parsing by an analyst.




























%201.png)







