Introduction to Fog Ransomware
As ransomware attacks continue to be launched at an alarming rate, Darktrace’s Threat Research team has identified that familiar strains like Akira, LockBit, and BlackBasta remain among the most prevalent threats impacting its customers, as reported in the First 6: Half-Year Threat Report 2024. Despite efforts by law agencies, like dismantling the infrastructure of cybercriminals and shutting down their operations [2], these groups continue to adapt and evolve.
As such, it is unsurprising that new ransomware variants are regularly being created and launched to get round law enforcement agencies and increasingly adept security teams. One recent example of this is Fog ransomware.
What is Fog ransomware?
Fog ransomware is strain that first appeared in the wild in early May 2024 and has been observed actively using compromised virtual private network (VPN) credentials to gain access to organization networks in the education sector in the United States.
Darktrace's detection of Fog Ransomware
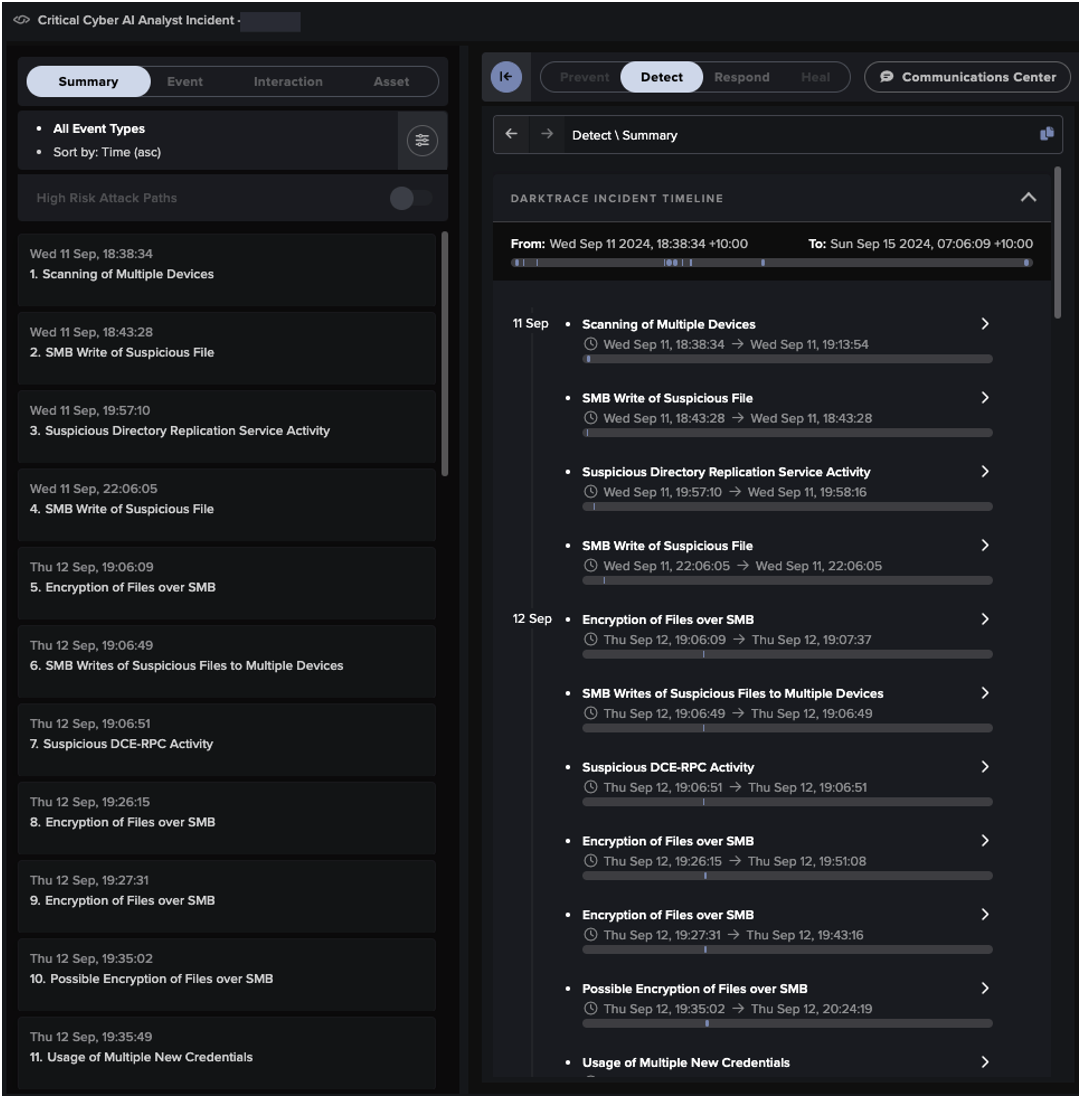
In June 2024, Darktrace observed instances of Fog ransomware across multiple customer environments. The shortest time observed from initial access to file encryption in these attacks was just 2 hours, underscoring the alarming speed with which these threat actors can achieve their objectives.
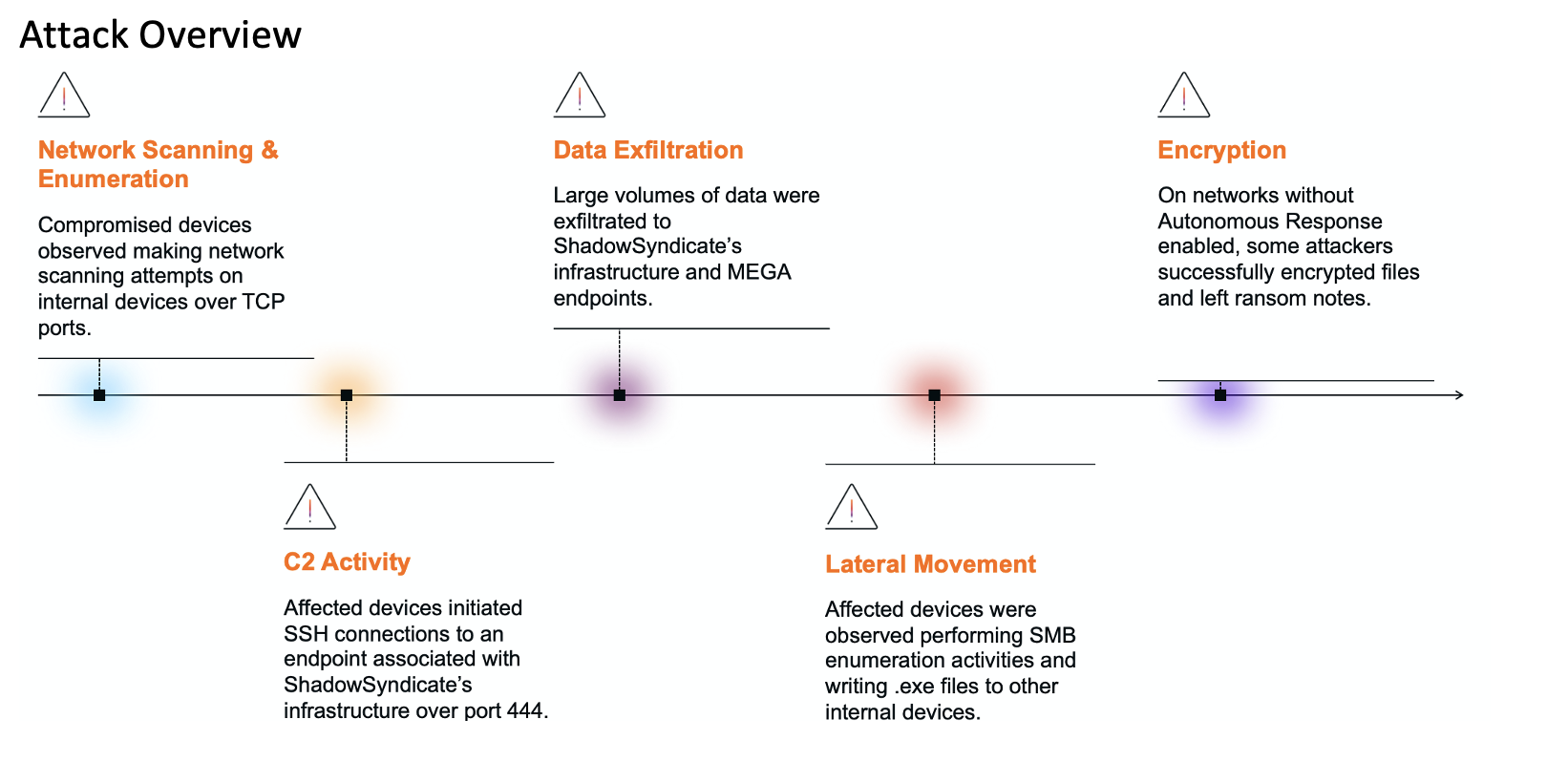
Darktrace identified key activities typical of a ransomware kill chain, including enumeration, lateral movement, encryption, and data exfiltration. In most cases, Darktrace was able to successfully halt the progression Fog attacks in their early stages by applying Autonomous Response actions such as quarantining affected devices and blocking suspicious external connections.
To effectively illustrate the typical kill chain of Fog ransomware, this blog focuses on customer environments that did not have Darktrace’s Autonomous Response enabled. In these cases, the attack progressed unchecked and reached its intended objectives until the customer received Darktrace’s alerts and intervened.
Darktrace’s Coverage of Fog Ransomware
Initial Intrusion
After actors had successfully gained initial access into customer networks by exploiting compromised VPN credentials, Darktrace observed a series of suspicious activities, including file shares, enumeration and extensive scanning. In one case, a compromised domain controller was detected making outgoing NTLM authentication attempts to another internal device, which was subsequently used to establish RDP connections to a Windows server running Hyper-V.
Given that the source was a domain controller, the attacker could potentially relay the NTLM hash to obtain a domain admin Kerberos Ticket Granting Ticket (TGT). Additionally, incoming NTLM authentication attempts could be triggered by tools like Responder, and NTLM hashes used to encrypt challenge response authentication could be abused by offline brute-force attacks.
Darktrace also observed the use of a new administrative credential on one affected device, indicating that malicious actors were likely using compromised privileged credentials to conduct relay attacks.
Establish Command-and-Control Communication (C2)
In many instances of Fog ransomware investigated by Darktrace’s Threat Research team, devices were observed making regular connections to the remote access tool AnyDesk. This was exemplified by consistent communication with the endpoint “download[.]anydesk[.]com” via the URI “/AnyDesk.exe”. In other cases, Darktrace identified the use of another remote management tool, namely SplashTop, on customer servers.
In ransomware attacks, threat actors often use such legitimate remote access tools to establish command-and-control (C2) communication. The use of such services not only complicates the identification of malicious activities but also enables attackers to leverage existing infrastructure, rather than having to implement their own.
Internal Reconnaissance
Affected devices were subsequently observed making an unusual number of failed internal connections to other internal locations over ports such as 80 (HTTP), 3389 (RDP), 139 (NetBIOS) and 445 (SMB). This pattern of activity strongly indicated reconnaissance scanning behavior within affected networks. A further investigation into these HTTP connections revealed the URIs “/nice ports”/Trinity.txt.bak”, commonly associated with the use of the Nmap attack and reconnaissance tool.
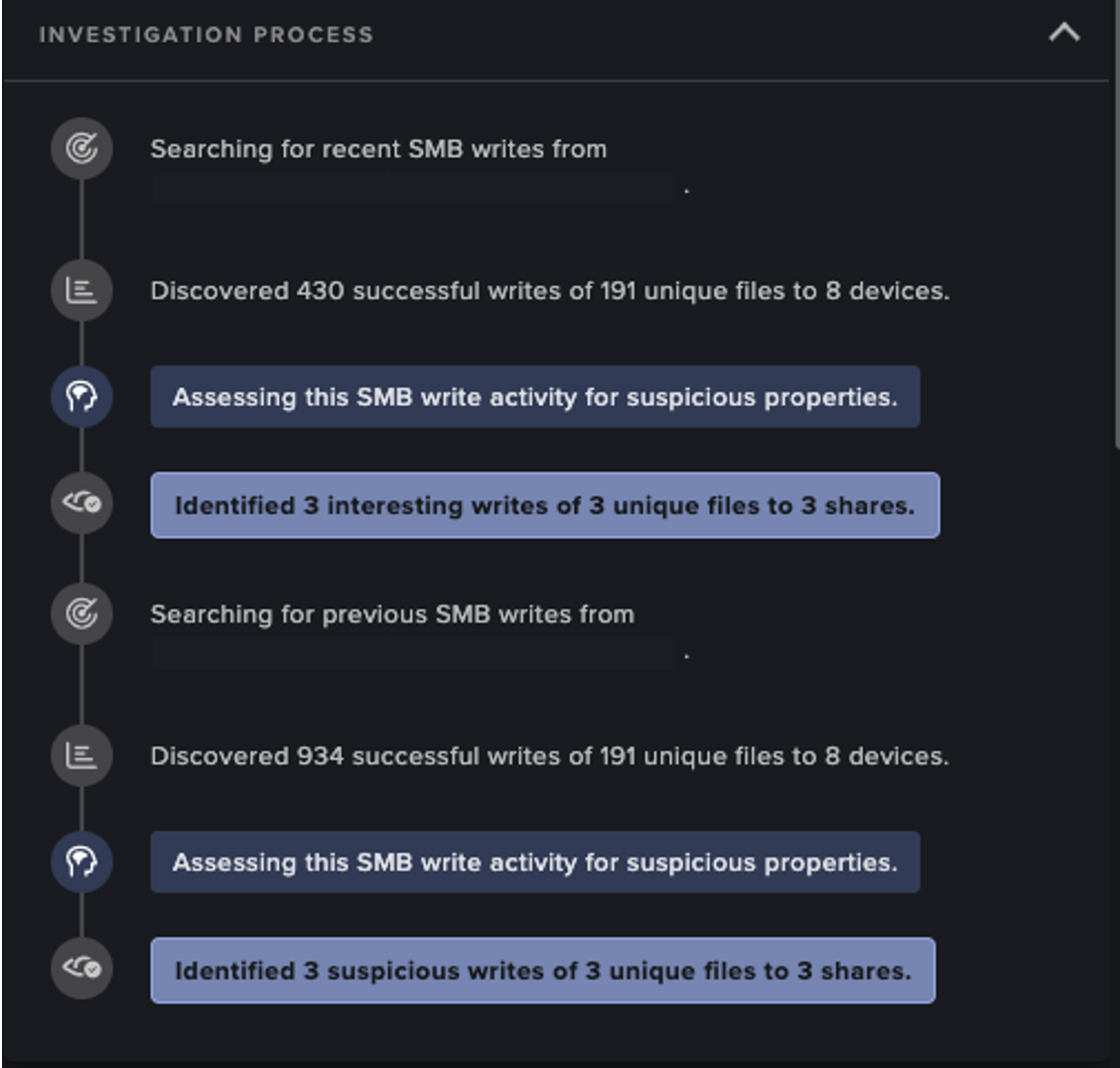
Simultaneously, some devices were observed engaging in SMB actions targeting the IPC$ share and the named pipe “srvsvc” on internal devices. Such activity aligns with the typical SMB enumeration tactics, whereby attackers query the list of services running on a remote host using a NULL session, a method often employed to gather information on network resources and vulnerabilities.
Lateral Movement
As attackers attempted to move laterally through affected networks, Darktrace observed suspicious RDP activity between infected devices. Multiple RDP connections were established to new clients, using devices as pivots to propagate deeper into the networks, Following this, devices on multiple networks exhibited a high volume of SMB read and write activity, with internal share drive file names being appended with the “.flocked” extension – a clear sign of ransomware encryption. Around the same time, multiple “readme.txt” files were detected being distributed across affected networks, which were later identified as ransom notes.
Further analysis of the ransom note revealed that it contained an introduction to the Fog ransomware group, a summary of the encryption activity that had been carried out, and detailed instructions on how to communicate with the attackers and pay the ransom.

Data Exfiltration
In one of the cases of Fog ransomware, Darktrace’s Threat Research team observed potential data exfiltration involving the transfer of internal files to an unusual endpoint associated with the MEGA file storage service, “gfs302n515[.]userstorage[.]mega[.]co[.]nz”.
This exfiltration attempt suggests the use of double extortion tactics, where threat actors not only encrypt victim’s data but also exfiltrate it to threaten public exposure unless a ransom is paid. This often increases pressure on organizations as they face the risk of both data loss and reputational damage caused by the release of sensitive information.
Darktrace’s Cyber AI Analyst autonomously investigated what initially appeared to be unrelated events, linking them together to build a full picture of the Fog ransomware attack for customers’ security teams. Specifically, on affected networks Cyber AI Analyst identified and correlated unusual scanning activities, SMB writes, and file appendages that ultimately suggested file encryption.


Safeguarding vulnerable sectors with real-time ransomware mitigation
As novel and fast-moving ransomware variants like Fog persist across the threat landscape, the time taken for from initial compromise to encryption has significantly decreased due to the enhanced skill craft and advanced malware of threat actors. This trend particularly impacts organizations in the education sector, who often have less robust cyber defenses and significant periods of time during which infrastructure is left unmanned, and are therefore more vulnerable to quick-profit attacks.
Traditional security methods may fall short against these sophisticated attacks, where stealthy actors evade detection by human-managed teams and tools. In these scenarios Darktrace’s AI-driven product suite is able to quickly detect and respond to the initial signs of compromise through autonomous analysis of any unusual emerging activity.
When Darktrace’s Autonomous Response capability was active, it swiftly mitigated emerging Fog ransomware threats by quarantining devices exhibiting malicious behavior to contain the attack and blocking the exfiltration of sensitive data, thus preventing customers from falling victim to double extortion attempts.
[related-resource]
Appendices
Credit to Qing Hong Kwa (Senior Cyber Analyst and Deputy Analyst Team Lead, Singapore) and Ryan Traill (Threat Content Lead)
Darktrace Model Detections:
- Anomalous Server Activity::Anomalous External Activity from Critical Network Device
- Anomalous Connection::SMB Enumeration
- Anomalous Connection::Suspicious Read Write Ratio and Unusual SMB
- Anomalous Connection::Uncommon 1 GiB Outbound
- Anomalous File::Internal::Additional Extension Appended to SMB File
- Compliance::Possible Cleartext LDAP Authentication
- Compliance::Remote Management Tool On Server
- Compliance::SMB Drive Write
- Compromise::Ransomware::SMB Reads then Writes with Additional Extensions
- Compromise::Ransomware::Possible Ransom Note Write
- Compromise::Ransomware::Ransom or Offensive Words Written to SMB
- Device::Attack and Recon Tools
- User::New Admin Credentials on Client
- Unusual Activity::Anomalous SMB Move & Write
- Unusual Activity::Internal Data Transfer
- Unusual Activity::Unusual External Data Transfer
- Unusual Activity::Enhanced Unusual External Data Transfer
Darktrace Model Detections:
- Antigena::Network::External Threat::Antigena Suspicious File Block
- Antigena::Network::External Threat::Antigena Suspicious File Pattern of Life Block
- Antigena::Network::External Threat::Antigena File then New Outbound Block
- Antigena::Network::External Threat::Antigena Ransomware Block
- Antigena::Network::External Threat::Antigena Suspicious Activity Block
- Antigena::Network::Significant Anomaly::Antigena Controlled and Model Breach
- Antigena::Network::Significant Anomaly::Antigena Enhanced Monitoring from Server Block
- Antigena::Network::Significant Anomaly::Antigena Breaches Over Time Block
- Antigena::Network::Significant Anomaly::Antigena Significant Server Anomaly Block
- Antigena::Network::Insider Threat::Antigena Internal Data Transfer Block
- Antigena::Network::Insider Threat::Antigena Large Data Volume Outbound Block
- Antigena::Network::Insider Threat::Antigena SMB Enumeration Block
AI Analyst Incident Coverage
- Encryption of Files over SMB
- Scanning of Multiple Devices
- SMB Writes of Suspicious Files
MITRE ATT&CK Mapping
(Technique Name) – (Tactic) – (ID) – (Sub-Technique of)
Data Obfuscation - COMMAND AND CONTROL - T1001
Remote System Discovery - DISCOVERY - T1018
SMB/Windows Admin Shares - LATERAL MOVEMENT - T1021.002 - T1021
Rename System Utilities - DEFENSE EVASION - T1036.003 - T1036
Network Sniffing - CREDENTIAL ACCESS, DISCOVERY - T1040
Exfiltration Over C2 Channel - EXFILTRATION - T1041
Data Staged - COLLECTION - T1074
Valid Accounts - DEFENSE EVASION, PERSISTENCE, PRIVILEGE ESCALATION, INITIAL ACCESS - T1078
Taint Shared Content - LATERAL MOVEMENT - T1080
File and Directory Discovery - DISCOVERY - T1083
Email Collection - COLLECTION - T1114
Automated Collection - COLLECTION - T1119
Network Share Discovery - DISCOVERY - T1135
Exploit Public-Facing Application - INITIAL ACCESS - T1190
Hardware Additions - INITIAL ACCESS - T1200
Remote Access Software - COMMAND AND CONTROL - T1219
Data Encrypted for Impact - IMPACT - T1486
Pass the Hash - DEFENSE EVASION, LATERAL MOVEMENT - T1550.002 - T1550
Exfiltration to Cloud Storage - EXFILTRATION - T1567.002 - T1567
Lateral Tool Transfer - LATERAL MOVEMENT - T1570
List of Indicators of Compromise (IoCs)
IoC – Type – Description
/AnyDesk.exe - Executable File - Remote Access Management Tool
gfs302n515[.]userstorage[.]mega[.]co[.]nz- Domain - Exfiltration Domain
*.flocked - Filename Extension - Fog Ransomware Extension
readme.txt - Text File - Fog Ransom Note
xql562evsy7njcsngacphcerzjfecwotdkobn3m4uxu2gtqh26newid[.]onion - Onion Domain - Threat Actor’s Communication Channel
References
[1] https://arcticwolf.com/resources/blog/lost-in-the-fog-a-new-ransomware-threat/
[2] https://intel471.com/blog/assessing-the-disruptions-of-ransomware-gangs
[3] https://www.pcrisk.com/removal-guides/30167-fog-ransomware
Get the latest insights on emerging cyber threats
This report explores the latest trends shaping the cybersecurity landscape and what defenders need to know in 2025.
.png)