As industrial environments modernize, IT and OT networks are converging to improve efficiency, but this connectivity also creates new attack paths. Previously isolated OT systems are now linked to IT and cloud assets, making them more accessible to attackers.
While organizations have traditionally relied on air gaps, firewalls, data diodes, and access controls to separate IT and OT, these measures alone aren’t enough. Threat actors often infiltrate IT/Enterprise networks first then exploit segmentation, compromising credentials, or shared IT/OT systems to move laterally, escalate privileges, and ultimately enter the OT network.
To defend against these threats, organizations must first ensure they have complete visibility across IT and OT environments.
Visibility: The first piece of the puzzle
Visibility is the foundation of effective industrial cybersecurity, but it’s only the first step. Without visibility across both IT and OT, security teams risk missing key alerts that indicate a threat targeting OT at their earliest stages.
For Attacks targeting OT, early stage exploits often originate in IT environments, adversaries perform internal reconnaissance among other tactics and procedures but then laterally move into OT first affecting IT devices, servers and workstations within the OT network. If visibility is limited, these threats go undetected. To stay ahead of attackers, organizations need full-spectrum visibility that connects IT and OT security, ensuring no early warning signs are missed.
However, visibility alone isn’t enough. More visibility also means more alerts, this doesn’t just make it harder to separate real threats from routine activity, but bogs down analysts who have to investigate all these alerts to determine their criticality.
Investigations: The real bottleneck
While visibility is essential, it also introduces a new challenge: Alert fatigue. Without the right tools, analysts are often occupied investigating alerts with little to no context, forcing them to manually piece together information and determine if an attack is unfolding. This slows response times and increases the risk of missing critical threats.

With siloed visibility across IT and OT each of these events shown above would be individually alerted by a detection engine with little to no context nor correlation. Thus, an analyst would have to try to piece together these events manually. Traditional security tools struggle to keep pace with the sophistication of these threats, resulting in an alarming statistic: less than 10% of alerts are thoroughly vetted, leaving organizations vulnerable to undetected breaches. As a result, incidents inevitably follow.
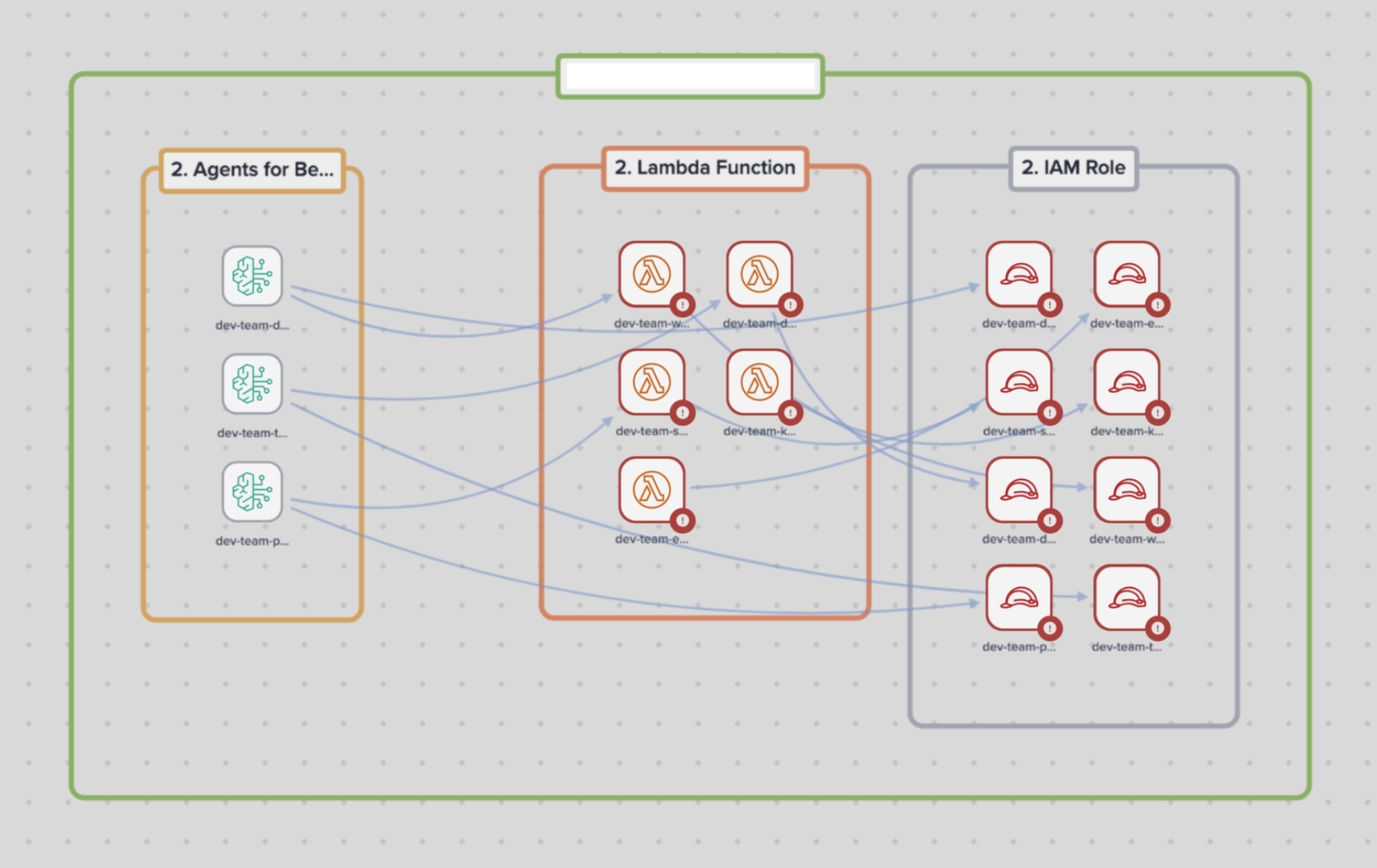
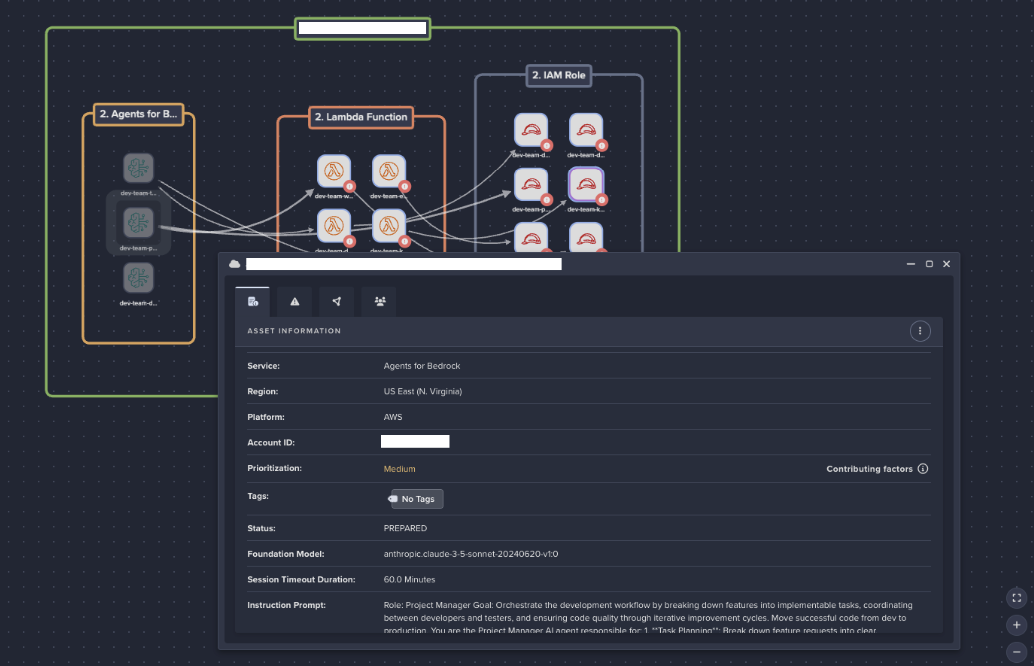
Darktrace’s Cyber AI Analyst uses AI-led investigations to improve workflows for analysts by automatically correlating alerts wherever they occur across both IT and OT. The multi-layered AI engine identifies high-priority incidents, and provides analysts with clear, actionable insights, reducing noise and highlighting meaningful threats. The AI significantly alleviates workloads, enabling teams to respond faster and more effectively before an attack escalates.
Overcoming organizational challenges across IT and OT
Beyond technical challenges like visibility and alert management, organizational dynamics further complicate IT-OT security efforts. Fundamental differences in priorities, workflows, and risk perspectives create challenges that can lead to misalignment between teams:
Non-transferable practices: IT professionals might assume that cybersecurity practices from IT environments can be directly applied to OT environments. This can lead to issues, as OT systems and workflows may not handle IT security processes as expected. It's crucial to recognize and respect the unique requirements and constraints of OT environments.
Segmented responsibilities: IT and OT teams often operate under separate organizational structures, each with distinct priorities, goals, and workflows. While IT focuses on data security, network integrity, and enterprise applications, OT prioritizes uptime, reliability, and physical processes.
Different risk perspectives: While IT teams focus on preventing cyber threats and regulatory violations, OT teams prioritize uptime and operational reliability making them drawn towards asset inventory tools that provide no threat detection capability.
Result: A combination of disparate and ineffective tools and misaligned teams can make any progress toward risk reduction at an organization seem impossible. The right tools should be able to both free up time for collaboration and prompt better communication between IT and OT teams where it is needed. However, different size operations structure their IT and OT teams differently which impacts the priorities for each team.
In real-world scenarios, small IT teams struggle to manage security across both IT and OT, while larger organizations with OT security teams face alert fatigue and numerous false positives slowing down investigations and hindering effective communication with the IT security teams.
By unifying visibility and investigations, Darktrace / OT helps organizations of all sizes detect threats earlier, streamline workflows, and enhance security across both IT and OT environments. The following examples illustrate how AI-driven investigations can transform security operations, improving detection, investigation, and response.
Before and after AI-led investigation
Before: Small manufacturing company
At a small manufacturing company, a 1-3 person IT team juggles everything from email security to network troubleshooting. An analyst might see unusual traffic through the firewall:
- Unusual repeated outbound traffic from an IP within their OT network destined to an unidentifiable external IP.
With no dedicated OT security tools and limited visibility into the industrial network, they don’t know what the internal device in question is, if it is beaconing to a malicious external IP, and what it may be doing to other devices within the OT network. Without a centralized dashboard, they must manually check logs, ask operators about changes, and hunt for anomalies across different systems.
After a day of investigation, they concluded the traffic was not to be expected activity. They stop production within their smaller OT network, update their firewall rules and factory reset all OT devices and systems within the blast radius of the IP device in question.
After: Faster, automated response with Cyber AI Analyst
With Darktrace / OT and Cyber AI Analyst, the IT team moves from reactive, manual investigations to proactive, automated threat detection:
- Cyber AI Analyst connects alerts across their IT and OT infrastructure temporally mapping them to attack frameworks and provides contextual analysis of how alerts are linked, revealing in real time attackers attempting lateral movement from IT to OT.
- A human-readable incident report explains the full scope of the incident, eliminating hours of manual investigation.
- The team is faster to triage as they are led directly to prioritized high criticality alerts, now capable of responding immediately instead of wasting valuable time hunting for answers.
By reducing noise, providing context, and automating investigations, Cyber AI Analyst transforms OT security, enabling small IT teams to detect, understand, and respond to threats—without deep OT cybersecurity expertise.
Before: Large critical infrastructure organization
In large critical infrastructure operations, OT and IT teams work in separate silos. The OT security team needs to quickly assess and prioritize alerts, but their system floods them with notifications:
- Multiple new device connected to the ICS network alerts
- Multiple failed logins to HMI detected
- Multiple Unusual Modbus/TCP commands detected
- Repeated outbound OT traffic to IT destinations
At first glance, these alerts seem important, but without context, it’s unclear whether they indicate a routine error, a misconfiguration, or an active cyber-attack. They might ask:
- Are the failed logins just a mistake, or a brute-force attempt?
- Is the outbound traffic part of a scheduled update, or data exfiltration?
Without correlation across events, the engineer must manually investigate each one—checking logs, cross-referencing network activity, and contacting operators—wasting valuable time. Meanwhile, if it’s a coordinated attack, the adversary may already be disrupting operations.
After: A new workflow with Cyber AI Analyst
With Cyber AI Analyst, the OT security team gets clear, automated correlation of security events, making investigations faster and more efficient:
- Automated correlation of OT threats: Instead of isolated alerts, Cyber AI Analyst stitches together related events, providing a single, high-confidence incident report that highlights key details.
- Faster time to meaning: The system connects anomalous behaviors (e.g., failed logins, unusual traffic from an HMI, and unauthorized PLC modifications) into a cohesive narrative, eliminating hours of manual log analysis.
- Prioritized and actionable alerts: OT security receives clear, ranked incidents, immediately highlighting what matters most.
- Rapid threat understanding: Security teams know within minutes whether an event is a misconfiguration or a cyber-attack, allowing for faster containment.
With Cyber AI Analyst, large organizations cut through alert noise, accelerate investigations, and detect threats faster—without disrupting OT operations.
An AI-led approach to industrial cybersecurity
Security vendors with a primary focus on IT may lack insight into OT threats. Even OT-focused vendors have limited visibility into IT device exploitation within OT networks, leading to failed ability to detect early indicators of compromise. A comprehensive solution must account for the unique characteristics of various OT environments.
In a world where industrial security is no longer just about protecting OT but securing the entire digital-physical ecosystem as it interacts with the OT network, Darktrace / OT is an AI-driven solution that unifies visibility across IT, IoT and OT, Cloud into one cohesive defense strategy.
Whether an attack originates from an external breach, an insider threat, a supply chain compromise, in the Cloud, OT, or IT domains Cyber AI Analyst ensures that security teams see the full picture - before disruption occurs.
[related-resource]
Learn more about Darktrace / OT
Unify IT and OT security under a single platform, ensuring seamless communication and protection for all interconnected devices.
.avif)