Introduction
Many organizations turn to AI to augment their email security only after a damaging attack serves as a wake-up call. Such was the case recently with an academic institution in the APAC region. The organization felt fully protected at the time, with spam protection, URL protection, and the full Mimecast package across the email realm. However, it was interested in understanding how Cyber AI might defend its inbox, and scheduled a conversation to learn more.
Two days before that conversation was due to take place, the company was hit by a Business Email Compromise. An attacker had taken over an internal Microsoft 365 account and sent a fraudulent invoice to the organization’s accounts department. The invoice, which contained subtly edited bank details, claimed to be from Siemens, one of the world’s leading automation technology companies. Given that Siemens was an established supplier, the attack succeeded – and the academic institution unwittingly paid over $60,000 into an attacker’s bank account.
The incident alerted this organization not only to the scale and severity of email attacks, but also the limitations in its existing security tools. The security team swiftly deployed Antigena Email, and the AI’s ability to neutralize the advanced attacks missed by other tools was immediately realized when the attacker tried again a week later.
On this occasion, with the AI now in place, unusual behavior on the compromised SaaS account together with the suspicious email activity caused several Darktrace models to fire, culminating in a 73% anomaly score and the decision to autonomously hold back the offending email. The below details the timeline of this attack, and how Darktrace was able to identify an attack where other security tools failed.
Patient Zero: the initial compromise
Darktrace first detected something was amiss when a SaaS login was seen from an unusual IP address located in the UAE.
Tue April 21 04:15:40 (local time)
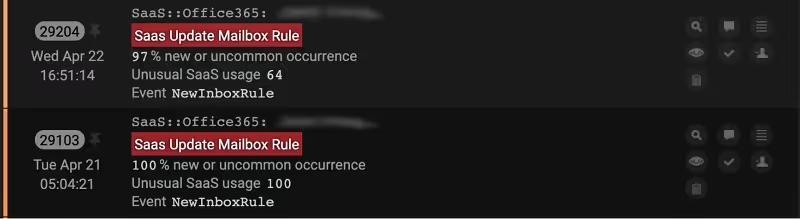
It then noticed a behavior commonly associated with Business Email Compromise – the creation of an inbox processing rule so that any incoming emails from the vendor would be deleted and redirected to the threat-actor.
Tue April 21st 05:04:21
Wed April 22nd 16:51:14
This initial compromise led to a very targeted spear phishing campaign. The attacker found an authentic email chain regarding an invoice from the domain siemens.com. Using the trusted supplier’s reputation, they copied the exact format of the invoice and then created a spoofed domain ‘siemesm.com’, intending to target the accounts team at the organization with a fresh invoice – but with one important detail changed – the bank details.
The attacker was careful. Before launching the attack, they sent a test email to the compromised account to ensure it was getting through. As seen below, this alerted Antigena Email with a 38% anomaly score.
The fraudulent invoice
The following morning, the attacker set up some fake correspondence between the newly created account and Patient Zero, before looping in the accounts team with a new request – this time, asking for $78,000. Again, the exchange appeared legitimate: from a well-known supplier, and with the apparent ratification of a trusted colleague.
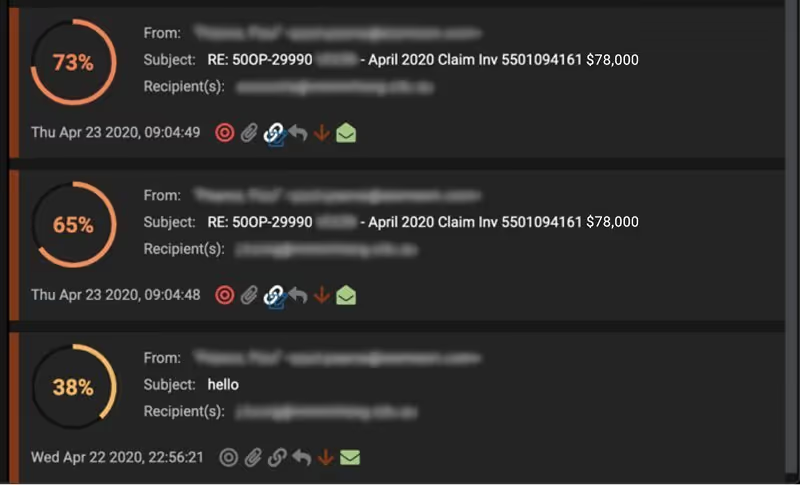
Here, we can see Antigena Email growing gradually more suspicious of this unusual behavior over time, with the highlighted ‘hold’ icon indicating that Antigena Email prevented the two offending emails from being delivered. The high anomaly score was influenced not only by the lack of previous correspondence between the two email users, but also the email rules that were made on the account itself the previous day. Furthermore, Cyber AI recognized the email as a fake reply: not a direct response to the email, but one which attempted to replicate it by copying and pasting correspondence from a separate email chain.
Realizing their initial attack had failed, the attacker then leveraged a technique known as ‘island hopping’, harvesting the company-wide contact list, and going on to launch a more generic phishing campaign to dozens of email users across the company – hoping in turn to compromise their accounts.
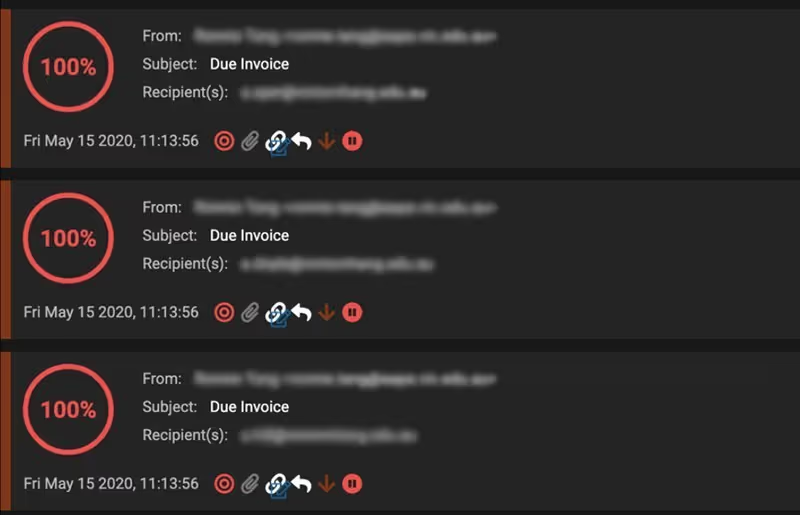
Again, Antigena Email deemed every one of these emails to be 100% anomalous and held them back in every case.
Whilst this was a relatively advanced attack with multiple stages, the techniques described above represent nothing exceptional – Antigena Email stops these kinds of attacks on a daily basis, in hundreds of organizations around the globe.
By deploying Cyber AI into their email environments, defenders not only have unrivalled visibility over internal and external mail flow, but the ability to stop targeted and sophisticated attacks, well before they can escalate into a crisis.



































