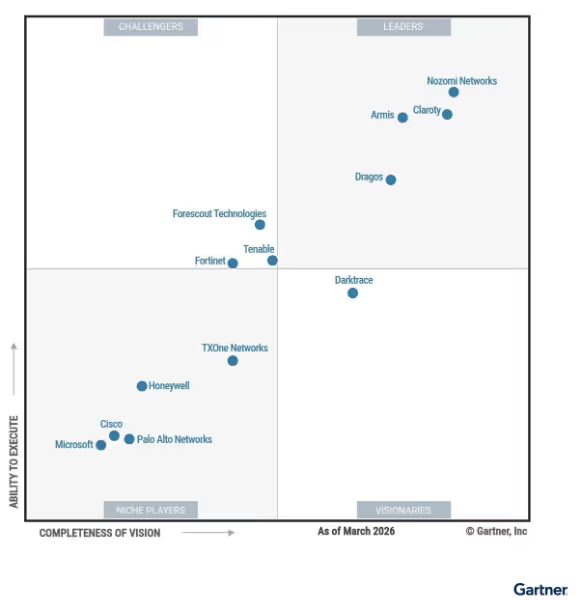
The Gartner® Magic Quadrant™ for CPS Protection Platforms provides an independent view of the vendors shaping this rapidly evolving market, evaluating how providers are helping organizations address the cybersecurity risks associated with increasingly connected operational technology and cyber-physical environments. Security and risk leaders use this research to better understand vendor positioning and to inform decisions as they modernize their Cyber Physical System (CPS) security strategies. We encourage organizations evaluating CPS security platforms to review the full report to gain a comprehensive view of the market.
Darktrace’s position as the only Visionary for the second consecutive year reflects the strength of our innovation, product execution, and long-term strategy for CPS security.
Darktrace / OT is built to address the realities of modern industrial defense, securing converged IT, OT, and IoT environments, applying Self-Learning AI to detect known, unknown, and novel threats, accelerating investigations and prioritizing risk based on operational impact. This unique approach supports the flexible deployment models required by complex critical infrastructure organizations.
Why Darktrace / OT stands apart in CPS security
As industrial environments continue to converge with enterprise infrastructure, security leaders are being asked to reduce cyber risk in systems where uptime, safety, and regulatory requirements limit traditional security approaches. Teams need to understand how risk develops across the environment, investigate threats with greater speed and clarity, and prioritize mitigation based on operational impact.
Darktrace / OT is built for that challenge. It combines cross-domain visibility, detection and investigation with Self-Learning AI, bespoke risk management beyond CVEs, and OT-relevant workflows that support both security outcomes and operational resilience.
Unified visibility across converged CPS environments
As critical infrastructure expands beyond traditional OT networks to include engineering workstations, HMIs, remote access pathways, enterprise systems, and cloud-linked infrastructure, teams need to understand how assets relate, where dependencies exist, and how exposure develops across domains.
Darktrace / OT provides unified visibility across OT, IT, IoT, and IoMT to help organizations understand cyber risk across connected industrial environments. By bringing telemetry together through capabilities such as Operational Overview, OT workflows, and deep protocol inspection, Darktrace helps engineers and security teams work from shared context and a more operationally relevant understanding of the environment they are defending.
Enhanced threat detection, investigation, and response powered by Self-Learning AI
While signatures can still provide value for known threats, they fail against insider misuse, zero-day exploits, and custom-built malware designed for targeted operations. Darktrace / OT uses Self-Learning AI to detect subtle deviations from normal behavior across industrial environments where threats often appear through abnormal communications, misuse of legitimate access, or suspicious device behavior rather than known malware. To improve incident investigation, Darktrace’s Cyber AI Analyst automatically correlates activity and produces contextual summaries to reduce manual triage effort and help teams move faster from alert to understanding.
Darktrace / OT further strengthens investigation and response through Expanded telemetry through NEXT for OT, extending visibility into operational endpoints such as engineering workstations and HMIs to support deeper root-cause analysis. Leveraging Self-Learning AI, Darktrace also enables autonomous response that can surgically contain anomalous activity while allowing industrial processes to continue operating normally. Organizations can customize response actions by device, device type, or network segment, with options ranging from fully autonomous enforcement to human confirmation workflows, helping security teams reduce operational disruption while maintaining control over response decisions.
Contextual risk prioritization based on operational relevance
Teams need the right tools to shift from reactive defense to proactively thinking about their security posture. However, most OT teams are stuck using IT-centric tools that don’t speak the language of industrial systems, are consistently overwhelmed with static CVE lists, and these tools offer no understanding of OT-specific protocols.
Darktrace / OT helps organizations move beyond static vulnerability lists by prioritizing cyber risk based on operational context. By incorporating asset criticality, network relationships, exploitability intelligence, behavioral telemetry, and attack path analysis, the platform helps teams understand which exposures could realistically impact operations. By correlating CVE severity, KEV data, MITRE techniques, and business impact, Darktrace enables more focused remediation decisions that support operational resilience, governance, and compliance initiatives such as IEC-62443.
Built for real-world deployment and enterprise alignment
Darktrace / OT is designed for the realities of industrial environments where flexible deployment across on-premises, hybrid, distributed, air-gapped and operationally sensitive networks is essential. The platform integrates with enterprise security ecosystems including SIEM, SOAR, CMDB, firewall, and governance tools to support broader security workflows. This enables OT security to align with enterprise programs while respecting operational constraints and improving collaboration between security and engineering teams.
Customer validation and platform recognition
In the last 12 months, Darktrace / OT has received a 4.8/5 rating on Gartner Peer Insights*. which we believe reflects strong customer confidence in the platform across critical infrastructure and industrial environments.
With this recognition, Darktrace is now positioned across multiple Gartner Magic Quadrants, including Leader positions in Network Detection and Response (NDR) and Email Security Platforms, reflecting the breadth of Darktrace’s ActiveAI Security Platform.

Continuing to advance the future of CPS security
We believe Darktrace’s recognition as the only Visionary for the second consecutive year reflects a clear direction: CPS security platforms need to help customers connect visibility to investigation, investigation to prioritization, and prioritization to real operational outcomes.
That remains our focus for Darktrace / OT.
As industrial environments continue to grow more connected, more complex, and more business-critical, we will continue to invest in the capabilities that help customers reduce uncertainty, strengthen resilience, and secure the systems that keep their operations running.
Gartner, Magic Quadrant for CPS Protection Platforms, Katell Thielemann, Ruggero Contu, Wam Voster, Sumit Rajput, 3 March 2026
Gartner does not endorse any vendor, product or service depicted in its research publications and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
GARTNER is a registered trademark and service mark of Gartner and Magic Quadrant and Peer Insights are a registered trademark, of Gartner, Inc. and/or its affiliates in the U.S. and internationally and are used herein with permission. All rights reserved.
Gartner Peer Insights content consists of the opinions of individual end users based on their own experiences with the vendors listed on the platform, should not be construed as statements of fact, nor do they represent the views of Gartner or its affiliates. Gartner does not endorse any vendor, product or service depicted in this content nor makes any warranties, expressed or implied, with respect to this content, about its accuracy or completeness, including any warranties of merchantability or fitness for a particular purpose.




















.avif)













.png)









%201.png)