The widespread and rapid adoption of Software-as-a-Service (SaaS) has opened up a breadth of security risks for IT teams. Unlike commercial off-the-shelf (COTS) software, SaaS security tends to be managed by third-party vendors rather than the end customer. Security teams therefore struggle with reduced visibility and control over these environments, and cyber-criminals have been quick to take advantage, launching a wave of cloud-based attacks, from Vendor Email Compromise to internal account hijacks.
Attackers often gain access to multiple accounts on the same domain, enabling them to attack from multiple angles, for example sending of hundreds of emails from one account, while maintaining persistence with another. This gives the hacker an opportunity to try multiple attack vectors, using tools native to the SaaS environment as well as external payloads.
While preventative controls such as Multi-Factor Authentication (MFA) provide an extra layer of protection, there are many techniques available to circumvent zero-trust approaches. Remote and flexible working is set to continue to varying degrees across many different regions and industries, so companies must now commit to securing their cloud architecture and developing proactive cyber security measures.
In this blog, we will analyze a persistent cyber-attack which targeted a real estate company in Europe and leveraged several compromised Microsoft 365 accounts. These SaaS takeovers are quickly becoming the new norm, but they are still misunderstood and poorly documented in the wider industry. Cyber AI detected every stage of this intrusion in real time, without the use of signatures or static rules.
A and B: Hijacking Microsoft 365 accounts
The organization had around 5,000 devices in its environment, with 1,000 active SaaS accounts. The timeline below shows how the threat actor leveraged the SaaS accounts of five different users to carry out the operation, as well as exploiting several other accounts on the final day.
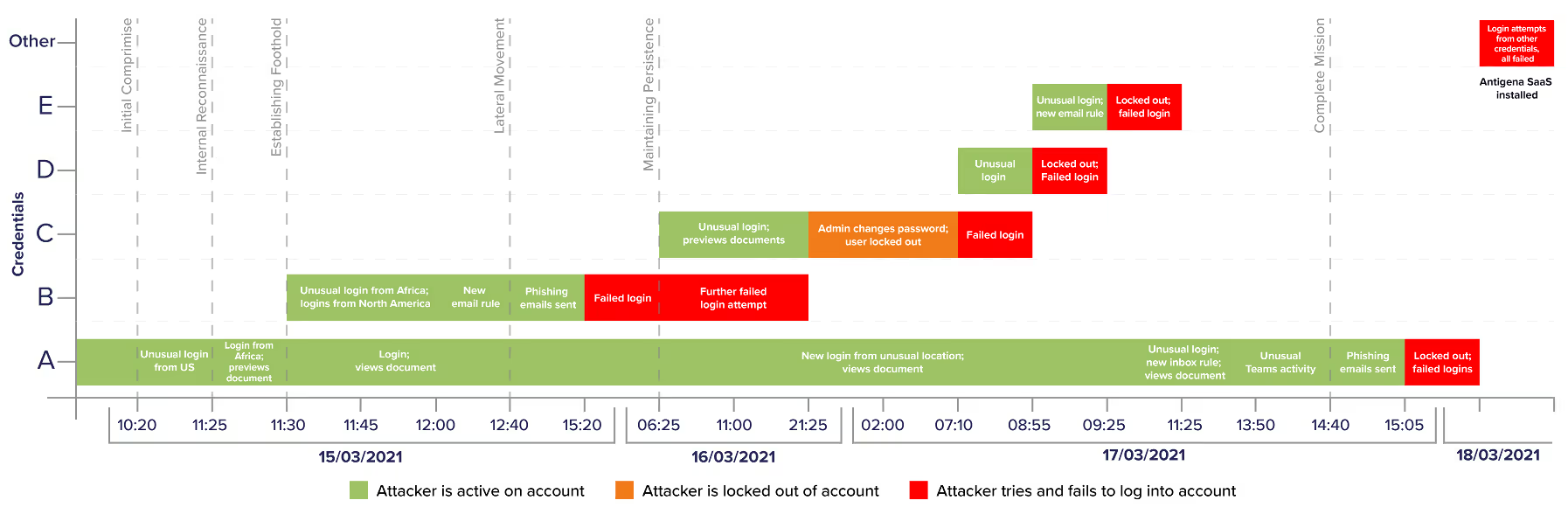
Figure 1: Diagram of the infection chain, which occurred over three days. On the fourth day, the attacker tried again but was unsuccessful.
The actor initially compromised at least two SaaS credentials – which we’ll refer to here simply as ‘account A’ and ‘account B’ – and logged in from several unusual geographical locations, presumably using a VPN. Darktrace detected this as unusual login events for the SaaS accounts.
In account A, the attacker was observed previewing files likely to contain customer information, but did not perform any other follow-up activity. In account B, they set a new inbox rule three hours after the initial compromise, resulting in a high-severity alert.
At around this time, the threat actor sent a number of phishing emails from account B: emails that appeared to be sharing a harmless and legitimate-looking folder on OneDrive. The link probably led to a fake Microsoft login page, similar to the below, which could have recorded the victims’ credentials and sent them directly back to the attacker.
Figure 2: A seemingly legitimate Microsoft login page.
The phishing attempt was detected by Antigena Email, Darktrace’s email security technology. Antigena was in passive mode at the time, and so was not configured to take action on these threatening emails. But taking into account the highly anomalous sender surge coupled with the unusual login locations, it would have autonomously intercepted all the emails, reducing the impact of the attack.
The attacker was subsequently locked out of account B. After this, they tried (and failed) to use a legacy user agent to bypass any MFA which may have been enforced on the account. Darktrace detected this as a suspicious login and blocked the attempt.
Accounts C, D and E: The threat develops
The next day, the actor logged into a new account (account C) from the same autonomous system number (ASN), indicating that the account had been infected by the OneDrive phishing emails. In other words, the attacker had leveraged account B to compromise new users in the organization and ensure multiple points of intrusion.
Darktrace detected each stage of this, piecing together the different events into one meaningful security narrative.
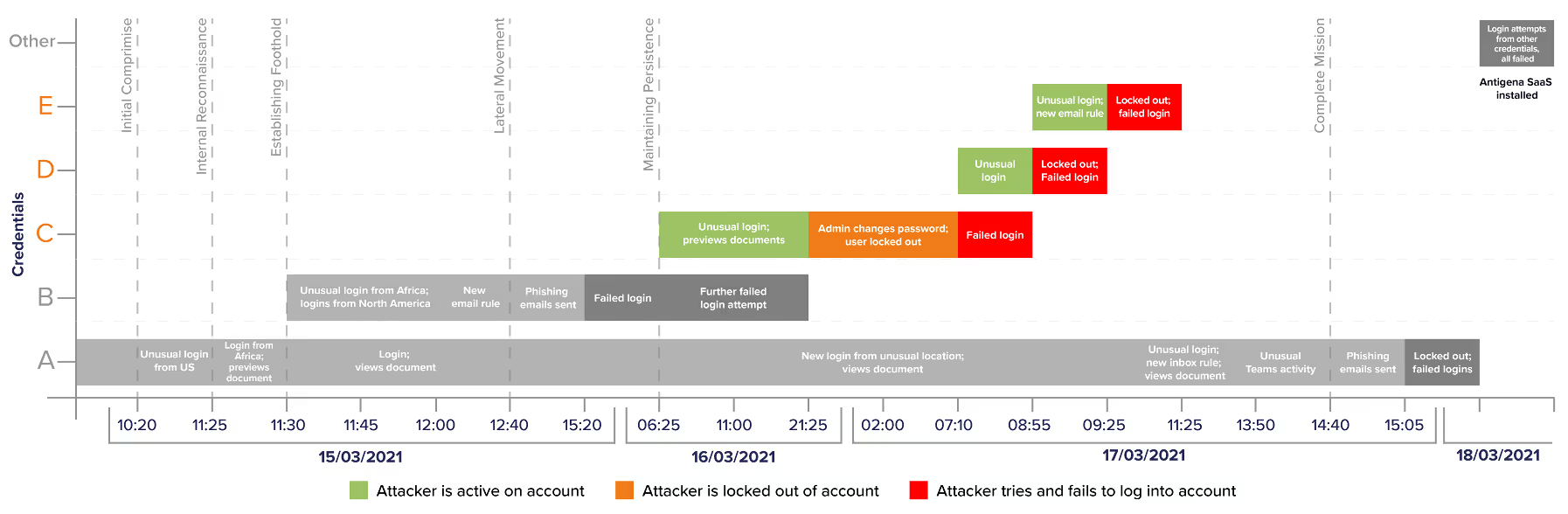
Figure 3: Anomalous activity from accounts C, D, and E.
Account C was then used to preview a file likely containing contact information.
After being locked out of account C when trying to log in the next day, the hacker worked their way through two more accounts (account D and account E), which they had hijacked in the previous phishing attempts. They were locked out each time after generating alerts due to the unusual logins and new inbox rules created around the same time.
A to Z: End of the line
Running out of options, the attacker decided to go back to account A and set a new inbox rule, using it to send new phishing emails with a link to a non-Microsoft cloud storage domain (Tresorit). Again, Darktrace recognized this as highly unusual behavior, and the hacker was promptly locked out of the account.
During this burst of activity, Darktrace also observed a Microsoft Teams session from one of the suspicious ASNs. This was likely a social engineering attempt and another possible attack vector. Microsoft Teams could have been leveraged to share a malicious link over instant message, extract sensitive information, or send spam internally and externally on the chat function.
The threat actor could have then used this to pivot across various applications and accounts, assuming that the company had a siloed security approach – with different tools for cloud, SaaS, email, and endpoint – and so could not pick up on the malicious cross-platform movement.
On the following day, the attacker attempted logins on multiple accounts again, but with no success. Cyber AI had pinpointed all the anomalous activity – no matter where it originated – and alerted the security team immediately.
SaaS attack under the microscope
Multi-account compromises can be incredibly persistent and are difficult for traditional security tools to identify. The hacker used several tactics to circumvent the customer’s existing email security products:
- The initial use of two compromised credentials – account A and account B – allowed the hacker to stay under the radar and not raise too much suspicion on a single account. Account A was kept quiet until other avenues had been exhausted.
- Activity was generated from multiple ASNs in at least three different geographical locations, probably utilizing a VPN: one in Africa where much of the activity originated, and two in North America, including some widely used ASNs which were highly unusual for the customer.
- The attacker entirely used Microsoft services until the final emails, choosing to ‘live off the land’ rather than sending links that may have been caught by gateways.
- The attacker logged into Microsoft Teams in their final movements – a fairly benign-looking event which could have been used to compromise more accounts and move laterally, and would have gone undetected.
Darktrace identified every stage of the attack – including spotting the anomalous ASNs – and launched an automatic, in-depth investigation with Cyber AI Analyst. The organization was thus able to take action before the damage was done.
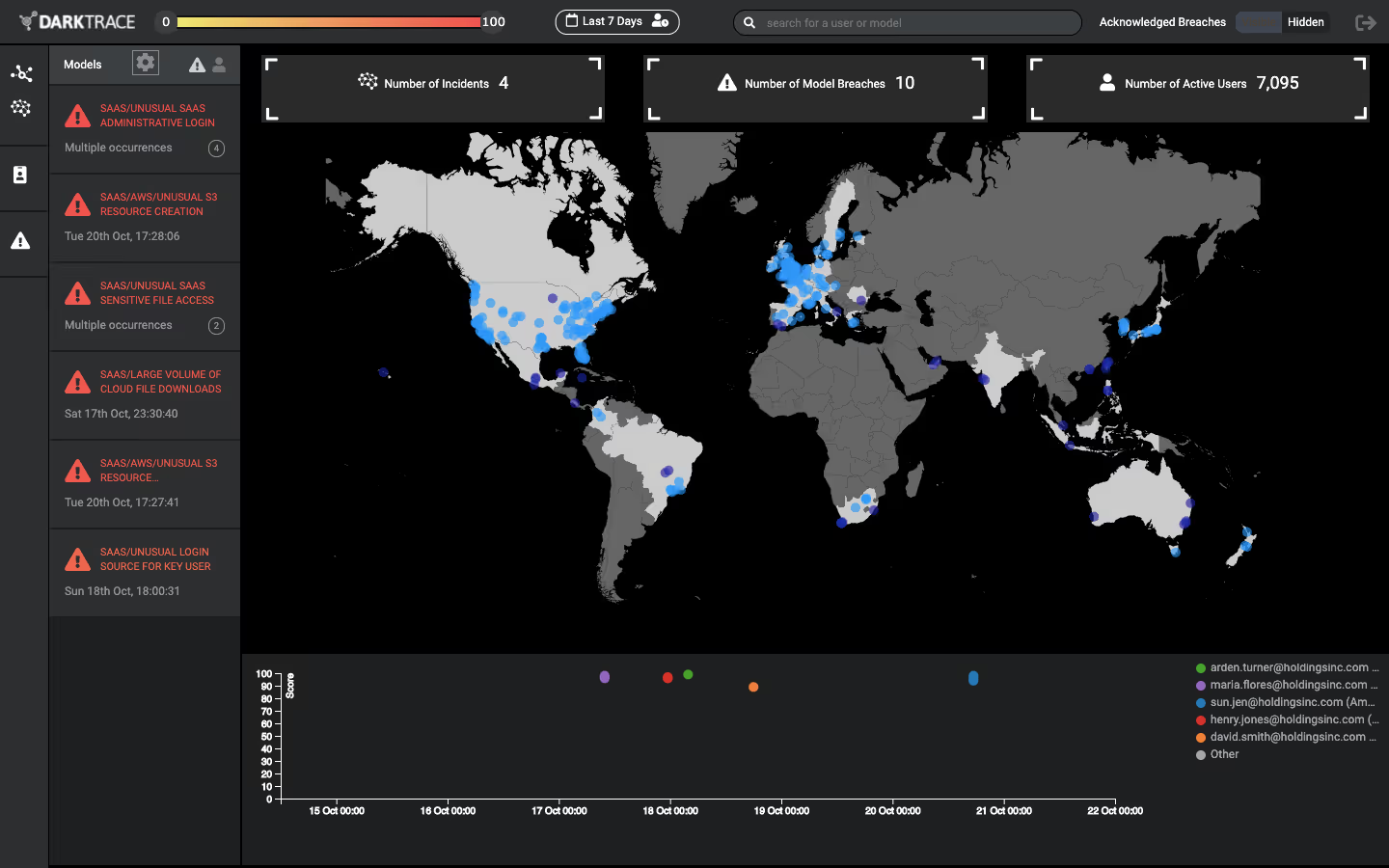
Figure 4: Darktrace’s SaaS console gives a clear overview of activity across all different applications.
ABCs of SaaS security
The approach of using various accounts to mount the offensive, while keeping one to maintain persistence, prolonged this intrusion. Such tactics will likely be seen again in the near future.
Tracking the number of factors involved in an attack with multiple credentials, multiple attack vectors, and multiple attacker-IPs, is a serious challenge. In these situations, it is essential to have a security solution which can detect activity across different applications, forming a unified and holistic understanding over the entire digital enterprise.
While not active in this case, Antigena SaaS would have taken autonomous action and prevented the threat from escalating by enforcing normal behavior, stopping the hacker from logging in from malicious infrastructure or performing any out-of-character SaaS actions, such as creating new inbox rules.
Following the intrusion, the company decided to adopt Antigena SaaS, which now mitigates their cloud security risks and guards against sensitive data loss and reputational damage.
Thanks to Darktrace analyst Daniel Gentle for his insights on the above threat find.
Darktrace model detections:
- SaaS / Compromise / Unusual Login and New Email Rule
- SaaS / Compliance / New Email Rule
- SaaS / Unusual Activity / Unusual External Source for SaaS Credential Use
- SaaS / Access / Suspicious Login Attempt
- Antigena Email: Unusual Login Location + Sender Surge





























%201.png)