Introduction
Darktrace and Microsoft entered a partnership in 2021 with a joint commitment to empower security defenders to free their organizations of cyber disruption. Darktrace AI complements Microsoft’s global reach and established intelligence community with its deep understanding of ‘self’ for individual organizations – learning ‘normal’ in order to prevent, detect, and respond to cyber-threats that represent a deviation from ‘normal’. With both products utilizing AI in different ways, the result for customers is the fusion of two security philosophies for a best-of-breed detection and response stack.
Now in 2023, Darktrace is proud to have this integration between its DETECT and RESPOND product families and Defender for Endpoint become part of the Microsoft Intelligence Security Association catalogue (MISA).
MISA is a global community dedicated to the shared mission of providing better security by integrating the very best solutions from across the digital landscape. Also see Darktrace’s membership for Darktrace for Defender for Email and Darktrace for Microsoft Sentinel.
Integrating Darktrace and Defender
Darktrace is designed to coordinate with Microsoft products, including hosting its email solution service on Azure and allowing customers using Sentinel to visualize and share incidents and AI Analyst investigations within their security information and event management (SIEM) tools. Integrating Microsoft Defender with Darktrace takes just minutes and can be set up using the System Configuration page of the deployment.
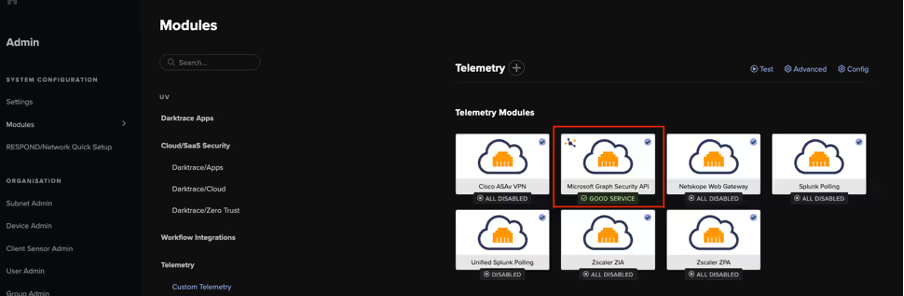
Additionally, Darktrace can retrieve data made available to it by Microsoft’s Graph Security API (Figure 2). When Defender Advanced Hunting (AH) is in use and a valid P2 license is integrated into Darktrace, it allows for more powerful API calls (Figure 3).
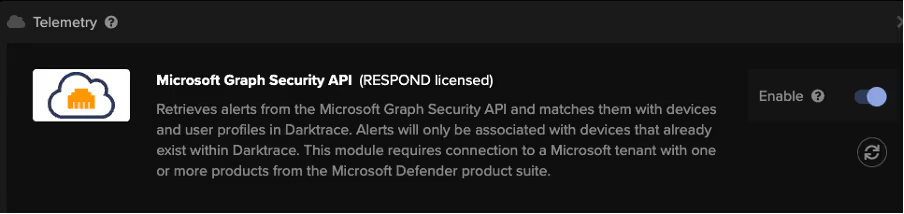

Defender can contextualize Darktrace information with endpoint insights, providing security teams visibility of the host-level detections surrounding network-level anomalies. Furthermore, if both Darktrace and Defender’s Advanced Hunting are in use and a compromise falls under the scope of both products, Darktrace can retrieve additional details, such as device operating system information (OS) and a list of common vulnerabilities and exposures (CVEs). This information is then presented in the Device Summary of the Threat Visualizer.
After the integration allows access to endpoint information, Darktrace learns from Defender and changes its behavior accordingly. When Defender identifies malicious activity, Darktrace simultaneously activates its integrated model breaches to show the Defender alert natively, ensuring consistency across platforms. This enables host-level anomaly detection; Darktrace applies its unsupervised machine learning to learn typical patterns of endpoint-level detections from Defender, to then alert based on deviations from regular Defender activity. Also using the integrated model breaches, Darktrace's AI Analyst can autonomously collate timestamp and device information from a Defender alert and investigate surrounding unusual activity from the suspect device, presenting a summary of all suspicious activity detected on the device.
Integration at Work
In December 2022, Darktrace DETECT identified a suspicious new user on an internal customer server. Immediately afterwards, an integration model breach was triggered based on Defender’s detection of suspicious activity on the same device.

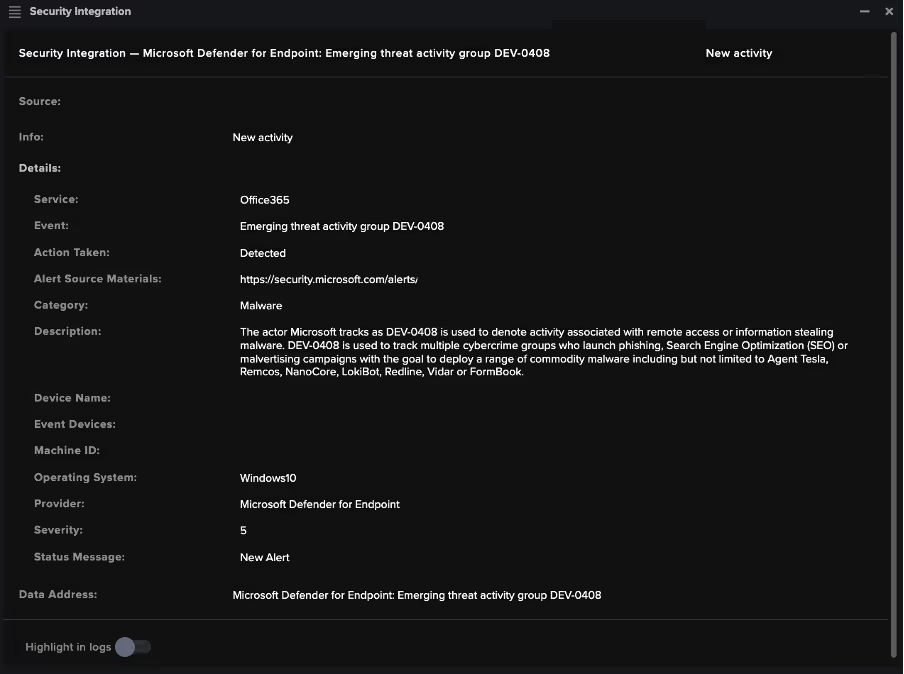
Independently, Darktrace detected a New User Agent to Internal Server event based on a connection between two internal devices. Prior to this, Defender had independently alerted signs of a threat actor group (DEV-0408), which was represented in Darktrace’s Event Logs. Darktrace can pull information from Defender directly into the UI to enhance its investigation and provide a unified view for the customer (Figure 5).

After Darktrace and Defender models both breached, Darktrace RESPOND acted instantly; the connections triggering the breaches were blocked and new connections to those endpoints on the detected port were suspended for the next two hours (Figure 6). This response proactively protected against subsequent suspicious activity, such as lateral movement. The device was later manually quarantined by the customer’s security team based on these detections and responses.
Conclusion
Darktrace’s Self-Learning AI works to understand customer environments and augment security teams with early warning detection and machine-speed response. Integration with Microsoft Defender helps to provide an even broader network security visibility by augmenting network-layer insights with host-specific information and activity. Defense in depth is crucial to a modern cyber security strategy and protection plan for organizations. Implementing the proven capabilities of Microsoft Defender alongside Darktrace’s innovative suite of products provides highly informed insights and holistic coverage from host to network to defend against a broad range of threats.
Thanks to Brianna Leddy, Director of Analysis, for her contributions to the above.
References
https://customerportal.darktrace.com/product-guides/main/defender-ah-intro-setup
https://customerportal.darktrace.com/product-guides/main/defender-ah-setup
https://customerportal.darktrace.com/product-guides/main/microsoft-security-introduction
https://darktrace.com/blog/integration-in-focus-bringing-machine-learning-to-third-party-edr-alerts







%201.png)





%201.png)





