Year after year, the holiday season witnesses an unprecedented exchange of cash in cyberspace, with American consumers alone projected to spend a record $143.7 billion on online holiday shopping in 2019.
And amid the desperation to take advantage of digital doorbusters, shoppers can find themselves racing between dozens of retail sites — all in pursuit of the dream deal.

Figure 1: The majority of holiday shopping is now done online. Data source: Adobe Digital Insights.
This frenzy of passwords, money, and credit card information changing hands over the winter months coalesces into the perfect storm for cyber-attacks. In November and December of last year, Darktrace observed a 128% rise in trojan attacks across our customer base relative to the previous two months. Such trojans, which leverage social engineering to mask their true nature, are often facilitated by “doppelganger” domains — slight variations of legitimate domain names that are used for malicious purposes. Indeed, doppelganger attacks in particular increased by 70% during the 2018 holidays, per Darktrace’s internal research.
For employees bombarded with time-sensitive discounts on their work devices and corporate email accounts, it is all too easy to miss the subtle signs of a doppelganger, while just a single click can cause an enterprise-wide breach. As a result, neither these employees nor traditional email security tools — which cannot be programmed in advance to spot the infinity of possible fake domains — are sufficient as a last line of defense. Rather, the only reliable way to sniff out convincing doppelgangers is Cyber AI. By learning the online behavior of each unique user and device that it protects, without preprogrammed rules or fixed IP blacklists, Cyber AI can distinguish between “naughty” and “nice” domains in real time.
Exposing a holiday doppelganger
Darktrace recently detected a doppelganger attack before it completed its objective: stealing sensitive financial information. Threat-actors typically attempt to recreate popular websites, and in this case, the duplicitous site masqueraded as an Amazon-associated page. Of course, the webpage had no connection to the genuine retail entity. Yet the targeted device’s firewall did not block it, since there is no way to anticipate all future doppelganger domains. And while the webpage also had misspellings and fake product images, the user — perhaps rushing to take advantage of a deal — did not notice.
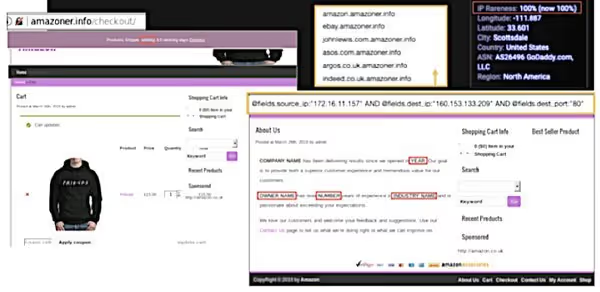
Figure 2: The doppelganger page — only a close examination reveals the irregularities highlighted above.
Most major businesses today utilize the standard security protocol “https://,” especially when payment information is involved, to encrypt the sensitive data being transferred. This measure alone does not guarantee a safe connection if the website itself was created or compromised by malicious actors — notwithstanding the digital padlock that appears beside HTTPS URLs. This doppelganger site, though, used the unencrypted HTTP protocol shown below (hence the unsecure padlock in Figure 2):
http://amazoner.info/checkout/
Because a significant percentage of legitimate websites still use HTTP, blocking connections to all such sites would be a mistake. By contrast, Darktrace Cyber AI, which had developed a nuanced understanding of the user’s online activity, correlated several weak indicators of compromise to flag the doppelganger as a potential threat.
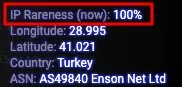
Figure 3: Darktrace flags the site as a 100% rare for the targeted user.
Once on the initial webpage, the user — engaged in what they believed to be regular online shopping — navigated to linked sites that were apparently associated with other popular clothing retailers:
ebay.amazoner.info
johnlewis.com.amazoner.info
asos.com.amazoner.inf
argos.co.uk.amazoner.info
indeed.co.uk.amazoner.info
Darktrace, again, determined that the escalating activity was highly unusual for the particular user. At this point, the security team was able to take the device offline for further investigation — before the user had entered any financial information.
’Tis the season to be secure
When it comes to what methods cyber-criminals will turn to next, the holiday season is full of unpredictability. No one knows what exactly the next doppelganger will look like, meaning that perimeter tools struggle to identify novel attacks before it’s too late.
As individual users, it is imperative to be wary of emails and ads that seem at all suspicious, even if it isn’t clear why. And when in doubt, it is always better to navigate directly to retail sites like Amazon from your browser, rather than clicking on an email link. The default disposition when shopping online — especially during the holidays — should be overcautiousness. Keep an eye out for broken language, typos, and design flaws that would all be rare on trustworthy retail sites, ensure URLs are legitimate before entering any information, and in general, trust your instincts when they sense something is amiss.
From an organizational standpoint, on the other hand, assume that employees won’t do any of the above. Human error is responsible for the vast majority of breaches, so expecting employees and conventional security tools to never allow attackers into the network is a recipe for compromise. Instead, to prepare for the inevitability of attack, what’s needed are Cyber AI tools that detect in-progress threats — not by predefining ‘bad’ but by understanding ‘self’. With self-learning Cyber AI, organizations are now readying themselves for the holidays, for sophisticated doppelgangers, and for the unpredictable.





























%201.png)







