Introduction: Spike in exploitation and post-exploitation activity affecting Palo Alto firewall devices
As the first line of defense for many organizations, perimeter devices such as firewalls are frequently targeted by threat actors. If compromised, these devices can serve as the initial point of entry to the network, providing access to vulnerable internal resources. This pattern of malicious behavior has become readily apparent within the Darktrace customer base. In 2024, Darktrace Threat Research analysts identified and investigated at least two major campaigns targeting internet-exposed perimeter devices. These included the exploitation of PAN-OS firewall exploitation via CVE 2024-3400 and FortiManager appliances via CVE 2024-47575.
More recently, at the end of November, Darktrace analysts observed a spike in exploitation and post-exploitation activity affecting, once again, Palo Alto firewall devices in the days following the disclosure of the CVE 2024-0012 and CVE-2024-9474 vulnerabilities.
Threat Research analysts had already been investigating potential exploitation of the firewalls’ management interface after Palo Alto published a security advisory (PAN-SA-2024-0015) on November 8. Subsequent analysis of data from Darktrace’s Security Operations Center (SOC) and external research uncovered multiple cases of Palo Alto firewalls being targeted via the likely exploitation of these vulnerabilities since November 13, through the end of the month. Although this spike in anomalous behavior may not be attributable to a single malicious actor, Darktrace Threat Research identified a clear increase in PAN-OS exploitation across the customer base by threat actors likely utilizing the recently disclosed vulnerabilities, resulting in broad patterns of post-exploitation activity.
How did exploitation occur?
CVE 2024-0012 is an authentication bypass vulnerability affecting unpatched versions of Palo Alto Networks Next-Generation Firewalls. The vulnerability resides in the management interface application on the firewalls specifically, which is written in PHP. When attempting to access highly privileged scripts, users are typically redirected to a login page. However, this can be bypassed by supplying an HTTP request where a Palo Alto related authentication header can be set to “off”. Users can supply this header value to the Nginx reverse proxy server fronting the application which will then send it without any prior processing [1].
CVE-2024-9474 is a privilege escalation vulnerability that allows a PAN-OS administrator with access to the management web interface to execute root-level commands, granting full control over the affected device [2]. When combined, these vulnerabilities enable unauthenticated adversaries to execute arbitrary commands on the firewall with root privileges.
Post-Exploitation Patterns of Activity
Darktrace Threat Research analysts examined potential indicators of PAN-OS software exploitation via CVE 2024-0012 and CVE-2024-9474 during November 2024. The investigation identified three main groupings of post-exploitation activity:
- Exploit validation and initial payload retrieval
- Command and control (C2) connectivity, potentially featuring further binary downloads
- Potential reconnaissance and cryptomining activity
Exploit Validation
Across multiple investigated customers, Darktrace analysts identified likely vulnerable PAN-OS devices conducting external network connectivity to bin services. Specifically, several hosts performed DNS queries for, and HTTP requests to Out-of-Band Application Security Testing (OAST) domains, such as csv2im6eq58ujueonqs0iyq7dqpak311i.oast[.]pro. These endpoints are commonly used by network administrators to harden defenses, but they are increasingly used by threat actors to verify successful exploitation of targeted devices and assess their potential for further compromise. Although connectivity involving OAST domains were prevalent across investigated incidents, this activity was not necessarily the first indicator observed. In some cases, device behavior involving OAST domains also occurred shortly after an initial payload was downloaded.

Initial Payload Retrieval
Following successful exploitation, affected devices commonly performed behaviors indicative of initial payload download, likely in response to incoming remote command execution. Typically, the affected PAN-OS host would utilize the command line utilities curl and Wget, seen via use of user agents curl/7.61.1 and Wget/1.19.5 (linux-gnu), respectively.
In some cases, the use of these command line utilities by the infected devices was considered new behavior. Given the nature of the user agents, interaction with the host shell suggests remote command execution to achieve the outgoing payload requests.
While additional binaries and scripts were retrieved in later stages of the post-exploitation activity in some cases, this set of behaviors and payloads likely represent initial persistence and execution mechanisms that will enable additional functionality later in the kill chain. During the investigation, Darktrace analysts noted the prevalence of shell script payload requests. Devices analyzed would frequently make HTTP requests over the usual destination port 80 using the command line URL utility (curl), as seen in the user-agent field.
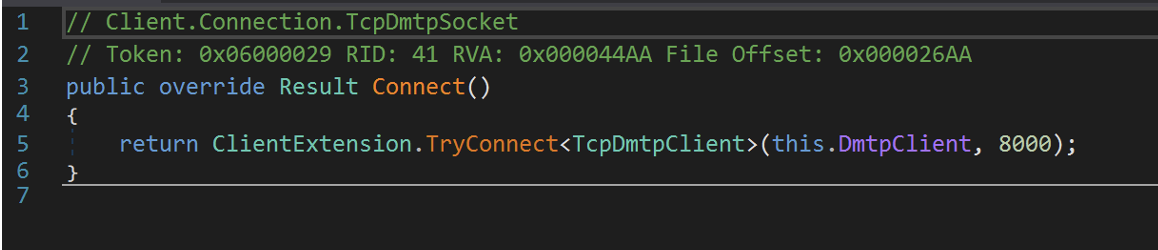
The observed URIs often featured requests for text files, such as “1.txt”, or shell scripts such as “y.sh”. Although packet capture (PCAP) samples were unavailable for review, external researchers have noted that the IP address hosting such “1.txt” files (46.8.226[.]75) serves malicious PHP payloads. When examining the contents of the “y.sh” shell script, Darktrace analysts noticed the execution of bash commands to upload a PHP-written web shell on the affected server.
![PCAP showing the client request and server response associated with the download of the y.sh script from 45.76.141[.]166. The body content of the HTTP response highlights a shebang command to run subsequent code as bash script. The content is base64 encoded and details PHP script for what appears to be a webshell that will likely be written to the firewall device.](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/675700c4a98f6ccec0f1a975_6756f988e443cb72200722b4_Screenshot%25202024-12-09%2520at%252014.06.53.avif)
While not all investigated cases saw initial shell script retrieval, affected systems would commonly make an external HTTP connection, almost always via Wget, for the Executable and Linkable Format (ELF) file “/palofd” from the rare external IP 38.180.147[.]18.
Such requests were frequently made without prior hostname lookups, suggesting that the process or script initiating the requests already contained the external IP address. Analysts noticed a consistent SHA1 hash present for all identified instances of “/palofd” downloads (90f6890fa94b25fbf4d5c49f1ea354a023e06510). Multiple open-source intelligence (OSINT) vendors have associated this hash sample with Spectre RAT, a remote access trojan with capabilities including remote command execution, payload delivery, process manipulation, file transfers, and data theft [3][4].

Several targeted customer devices were observed initiating TLS/SSL connections to rare external IPs with self-signed TLS certificates following exploitation. Model data from across the Darktrace fleet indicated some overlap in JA3 fingerprints utilized by affected PAN-OS devices engaging in the suspicious TLS activity. Although JA3 hashes alone cannot be used for process attribution, this evidence suggests some correlation of source process across instances of PAN-OS exploitation.
These TLS/SSL sessions were typically established without the specification of a Server Name Indication (SNI) within the TLS extensions. The SNI extension prevents servers from supplying an incorrect certificate to the requesting client when multiple sites are hosted on the same IP. SSL connectivity without SNI specification suggests a potentially malicious running process as most software establishing TLS sessions typically supply this information during the handshake. Although the encrypted nature of the connection prevented further analysis of the payload packets, external sources note that JavaScript content is transmitted during these sessions, serving as initial payloads for the Sliver C2 platform using Wget [5].
C2 Communication and Additional Payloads
Following validation and preliminary post-compromise actions, examined hosts would commonly initiate varying forms of C2 connectivity. During this time, devices were frequently detected making further payload downloads, likely in response to directives set within C2 communications.
Palo Alto firewalls likely exploited via the newly disclosed CVEs would commonly utilize the Sliver C2 platform for external communication. Sliver’s functionality allows for different styles and formatting for communication. An open-source alternative to Cobalt Strike, this framework has been increasingly popular among threat actors, enabling the generation of dynamic payloads (“slivers”) for multiple platforms, including Windows, MacOS, Linux.
These payloads allow operators to establish persistence, spawn new shells, and exfiltrate data. URI patterns and PCAPs analysis yielded evidence of both English word type encoding within Sliver and Gzip formatting.
For example, multiple devices contacted the Sliver-linked IP address 77.221.158[.]154 using HTTP to retrieve Gzip files. The URIs present for these requests follow known Sliver Gzip formatted communication patterns [6]. Investigations yielded evidence of both English word encoding within Sliver, identified through PCAP analysis, and Gzip formatting.
![Sample of URIs observed in Advanced Searchhighlighting HTTP requests to 77.221.158[.]154 for Gzip content suggest of Sliver communication.](https://cdn.prod.website-files.com/626ff4d25aca2edf4325ff97/6757623084734b0dbf6418e4_675761ed5dcf48e9b0b0befb_Screenshot%25202024-12-09%2520at%25201.31.31%25E2%2580%25AFPM.avif)

External connectivity during this phase also featured TCP connection attempts over uncommon ports for common application protocols. For both Sliver and non-Sliver related IP addresses, devices utilized destination ports such as 8089, 3939, 8880, 8084, and 9999 for the HTTP protocol. The use of uncommon destination ports may represent attempts to avoid detection of connectivity to rare external endpoints. Moreover, some external beaconing within included URIs referencing the likely IP of the affected device. Such behavior can suggest the registration of compromised devices with command servers.
Targeted devices also proceeded to download additional payloads from rare external endpoints as beaconing/C2 activity was ongoing. For example, the newly registered domain repositorylinux[.]org (IP: 103.217.145[.]112) received numerous HTTP GET requests from investigated devices throughout the investigation period for script files including “linux.sh” and “cron.sh”. Young domains, especially those that present as similar to known code repositories, tend to host harmful content. Packet captures of the cron.sh file reveal commands within the HTTP body content involving crontab operations, likely to schedule future downloads. Some hosts that engaged in connectivity to the fake repository domain were later seen conducting crypto-mining connections, potentially highlighting the download of miner applications from the domain.
Additional payloads observed during this time largely featured variations of shell scripts, PHP content, and/or executables. Typically, shell scripts direct the device to retrieve additional content from external servers or repositories or contain potential configuration details for subsequent binaries to run on the device. For example, the “service.sh” retrieves a tar-compressed archive, a configuration JSON file as well as a file with the name “solr” from GitHub, potentially associated with the Apache Solr tool used for enterprise search. These could be used for further enumeration of the host and/or the network environment. PHP scripts observed may involve similar web shell functionality and were retrieved from both rare external IPs identified as well by external researchers [7]. Darktrace also detected the download of octet-stream data occurring mid-compromise from an Amazon Web Services (AWS) S3 bucket. Although no outside research confirmed the functionality, additional executable downloads for files such as “/initd”(IP: 178.215.224[.]246) and “/x6” (IP: 223.165.4[.]175) may relate to tool ingress, further Trojan/backdoor functionality, or cryptocurrency mining.

Reconnaissance and Cryptomining
Darktrace analysts also noticed additional elements of kill chain operations from affected devices after periods of initial exploit activity. Several devices initiated TCP connections to endpoints affiliated with cryptomining pools such as us[.]zephyr[.]herominers[.]com and xmrig[.]com. Connectivity to these domains indicates likely successful installation of mining software during earlier stages of post-compromise activity. In a small number of instances, Darktrace observed reconnaissance and lateral movement within the time range of PAN-OS exploitation. Firewalls conducted large numbers of internal connectivity attempts across several critical ports related to privileged protocols, including SMB and SSH. Darktrace detected anonymous NTLM login attempts and new usage of potential PAN-related credentials. These behaviors likely constitute attempts at lateral movement to adjacent devices to further extend network compromise impact.

Conclusion
Darktrace Threat Research and SOC analysts increasingly detect spikes in malicious activity on internet-facing devices in the days following the publication of new vulnerabilities. The latest iteration of this trend highlighted how threat actors quickly exploited Palo Alto firewall using authentication bypass and remote command execution vulnerabilities to enable device compromise. A review of the post-exploitation activity during these events reveals consistent patterns of perimeter device exploitation, but also some distinct variations.
Prior campaigns targeting perimeter devices featured activity largely confined to the exfiltration of configuration data and some initial payload retrieval. Within the current campaign, analysts identified a broader scope post-compromise activity consisting not only of payloads downloads but also extensive C2 activity, reconnaissance, and coin mining operations. While the use of command line tools like curl featured prominently in prior investigations, devices were seen retrieving a generally wider array of payloads during the latest round of activity. The use of the Sliver C2 platform further differentiates the latest round of PAN-OS compromises, with evidence of Sliver activity in about half of the investigated cases.
Several of the endpoints contacted by the infected firewall devices did not have any OSINT associated with them at the time of the attack. However, these indicators were noted as unusual for the devices according to Darktrace based on normal network traffic patterns. This reality further highlights the need for anomaly-based detection that does not rely necessarily on known indicators of compromise (IoCs) associated with CVE exploitation for detection. Darktrace’s experience in 2024 of multiple rounds of perimeter device exploitation may foreshadow future increases in these types of comprise operations.
Credit to Adam Potter (Senior Cyber Analyst), Alexandra Sentenac (Senior Cyber Analyst), Emma Foulger (Principal Cyber Analyst) and the Darktrace Threat Research team.

Get the latest insights on emerging cyber threats
Attackers are adapting, are you ready? This report explores the latest trends shaping the cybersecurity landscape and what defenders need to know in 2025.
- Identity-based attacks: How attackers are bypassing traditional defenses
- Zero-day exploitation: The rise of previously unknown vulnerabilities
- AI-driven threats: How adversaries are leveraging AI to outmaneuver security controls
Stay ahead of evolving threats with expert analysis from Darktrace. Download the report here.
References
[1]: https://labs.watchtowr.com/pots-and-pans-aka-an-sslvpn-palo-alto-pan-os-cve-2024-0012-and-cve-2024-9474/
[2]: https://security.paloaltonetworks.com/CVE-2024-9474
[3]: https://threatfox.abuse[.]ch/ioc/1346254/
[4]:https://www.virustotal.com/gui/file/4911396d80baff80826b96d6ea7e54758847c93fdbcd3b86b00946cfd7d1145b/detection
[5]: https://arcticwolf.com/resources/blog/arctic-wolf-observes-threat-campaign-targeting-palo-alto-networks-firewall-devices/
[6] https://www.immersivelabs.com/blog/detecting-and-decrypting-sliver-c2-a-threat-hunters-guide
[7] https://arcticwolf.com/resources/blog/arctic-wolf-observes-threat-campaign-targeting-palo-alto-networks-firewall-devices/
Appendices
Darktrace Model Alerts
Anomalous Connection / Anomalous SSL without SNI to New External
Anomalous Connection / Application Protocol on Uncommon Port
Anomalous Connection / Multiple Failed Connections to Rare Endpoint
Anomalous Connection / Multiple HTTP POSTs to Rare Hostname
Anomalous Connection / New User Agent to IP Without Hostname
Anomalous Connection / Posting HTTP to IP Without Hostname
Anomalous Connection / Rare External SSL Self-Signed
Anomalous File / EXE from Rare External Location
Anomalous File / Incoming ELF File
Anomalous File / Mismatched MIME Type From Rare Endpoint
Anomalous File / Multiple EXE from Rare External Locations
Anomalous File / New User Agent Followed By Numeric File Download
Anomalous File / Script from Rare External Location
Anomalous File / Zip or Gzip from Rare External Location
Anomalous Server Activity / Rare External from Server
Compromise / Agent Beacon (Long Period)
Compromise / Agent Beacon (Medium Period)
Compromise / Agent Beacon to New Endpoint
Compromise / Beacon for 4 Days
Compromise / Beacon to Young Endpoint
Compromise / Beaconing Activity To External Rare
Compromise / High Priority Tunnelling to Bin Services
Compromise / High Volume of Connections with Beacon Score
Compromise / HTTP Beaconing to New IP
Compromise / HTTP Beaconing to Rare Destination
Compromise / Large Number of Suspicious Failed Connections
Compromise / Large Number of Suspicious Successful Connections
Compromise / Slow Beaconing Activity To External Rare
Compromise / SSL Beaconing to Rare Destination
Compromise / Suspicious Beaconing Behavior
Compromise / Suspicious File and C2
Compromise / Suspicious HTTP and Anomalous Activity
Compromise / Suspicious TLS Beaconing To Rare External
Compromise / Sustained SSL or HTTP Increase
Compromise / Sustained TCP Beaconing Activity To Rare Endpoint
Device / Initial Attack Chain Activity
Device / New User Agent
MITRE ATT&CK Mapping
Tactic – Technique
INITIAL ACCESS – Exploit Public-Facing Application
RESOURCE DEVELOPMENT – Malware
EXECUTION – Scheduled Task/Job (Cron)
EXECUTION – Unix Shell
PERSISTENCE – Web Shell
DEFENSE EVASION – Masquerading (Masquerade File Type)
DEFENSE EVASION - Deobfuscate/Decode Files or Information
CREDENTIAL ACCESS – Brute Force
DISCOVERY – Remote System Discovery
COMMAND AND CONTROL – Ingress Tool Transfer
COMMAND AND CONTROL – Application Layer Protocol (Web Protocols)
COMMAND AND CONTROL – Encrypted Channel
COMMAND AND CONTROL – Non-Standard Port
COMMAND AND CONTROL – Data Obfuscation
IMPACT – Resource Hijacking (Compute)
List of IoCs
IoC – Type – Description
- sys.traceroute[.]vip – Hostname - C2 Endpoint
- 77.221.158[.]154 – IP - C2 Endpoint
- 185.174.137[.]26 – IP - C2 Endpoint
- 93.113.25[.]46 – IP - C2 Endpoint
- 104.131.69[.]106 – IP - C2 Endpoint
- 95.164.5[.]41 – IP - C2 Endpoint
- bristol-beacon-assets.s3.amazonaws[.]com – Hostname - Payload Server
- img.dxyjg[.]com – Hostname - Payload Server
- 38.180.147[.]18 – IP - Payload Server
- 143.198.1[.]178 – IP - Payload Server
- 185.208.156[.]46 – IP - Payload Server
- 185.196.9[.]154 – IP - Payload Server
- 46.8.226[.]75 – IP - Payload Server
- 223.165.4[.]175 – IP - Payload Server
- 188.166.244[.]81 – IP - Payload Server
- bristol-beaconassets.s3[.]amazonaws[.]com/Y5bHaYxvd84sw – URL - Payload
- img[.]dxyjg[.]com/KjQfcPNzMrgV – URL - Payload
- 38.180.147[.]18/palofd – URL - Payload
- 90f6890fa94b25fbf4d5c49f1ea354a023e06510 – SHA1 - Associated to file /palofd
- 143.198.1[.]178/7Z0THCJ – URL - Payload
- 8d82ccdb21425cf27b5feb47d9b7fb0c0454a9ca – SHA1 - Associated to file /7Z0THCJ
- fefd0f93dcd6215d9b8c80606327f5d3a8c89712 – SHA1 - Associated to file /7Z0THCJ
- e5464f14556f6e1dd88b11d6b212999dd9aee1b1 – SHA1 - Associated to file /7Z0THCJ
- 143.198.1[.]178/o4VWvQ5pxICPm – URL - Payload
- 185.208.156[.]46/lUuL095knXd62DdR6umDig – URL - Payload
- 185.196.9[.]154/ykKDzZ5o0AUSfkrzU5BY4w – URL - Payload
- 46.8.226[.]75/1.txt – URL - Payload
- 223.165.4[.]175/x6 – URL - Payload
- 45.76.141[.]166/y.sh – URL - Payload
- repositorylinux[.]org/linux.sh – URL - Payload
- repositorylinux[.]org/cron.sh – URL - Payload