Update: On January 26, 2023, the Hive ransomware group was dismantled and servers associated with the sale of the ransomware were taken offline following an investigation by the FBI, German law enforcement and the National Crime Agency (NCA). The activity detailed in this blog took place in 2022, whilst the group was still active.
RaaS in Cyber Security
The threat of ransomware continues to be a constant concern for security teams across the cyber threat landscape. With the growing popularity of Ransomware-as-a-Service (RaaS), it is becoming more and more accessible for even inexperienced would-be attackers. As a result of this low barrier to entry, the volume of ransomware attacks is expected to increase significantly.
What’s more, RaaS is a highly tailorable market in which buyers can choose from varied kits and features to use in their ransomware deployments meaning attacks will rarely behave the same. To effectively detect and safeguard against these differentiations, it is crucial to implement security measures that put the emphasis on detecting anomalies and focusing on deviations in expected behavior, rather than relying on depreciated indicators of compromise (IoC) lists or playbooks that focus on attack chains unable to keep pace with the increasing speed of ransomware evolution.
In early 2022, Darktrace DETECT/Network™ identified several instances of Hive ransomware on the networks of multiple customers. Using its anomaly-based detection, Darktrace was able to successfully detect the attacks and multiple stages of the kill chain, including command and control (C2) activity, lateral movement, data exfiltration, and ultimately data encryption and the writing of ransom notes.
Hive Ransomware
Hive ransomware is a relatively new strain that was first observed in the wild in June 2021. It is known to target a variety of industries including healthcare, energy providers, and retailers, and has reportedly attacked over 1,500 organizations, collecting more than USD 100m in ransom payments [1].
Hive is distributed via a RaaS model where its developers update and maintain the code, in return for a percentage of the eventual ransom payment, while users (or affiliates) are given the tools to carry out attacks using a highly sophisticated and complex malware they would otherwise be unable to use. Hive uses typical tactics, techniques and procedures (TTPs) associated with ransomware, though they do vary depending on the Hive affiliate carrying out the attack.
In most cases a double extortion attack is carried out, whereby data is first exfiltrated and then encrypted before a ransom demand is made. This gives attackers extra leverage as victims are at risk of having their sensitive data leaked to the public on websites such as the ‘HiveLeaks’ TOR website.
Attack Timeline
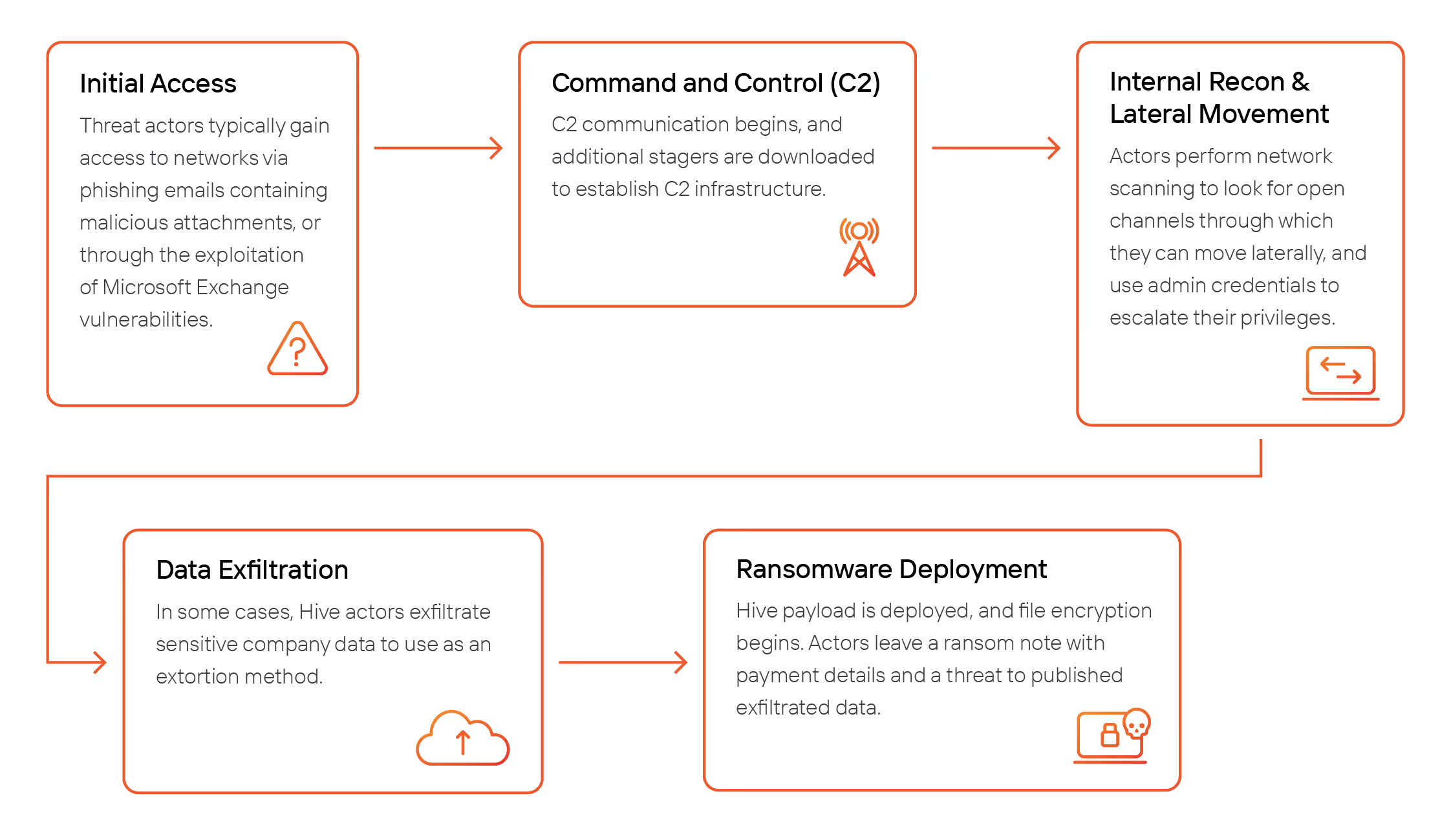
Owing to the highly customizable nature of RaaS, the tactics and methods employed by Hive actors are expected to differ on a case-by-case basis. Nonetheless in the majority of Hive ransomware incidents identified on Darktrace customer environments, Darktrace DETECT observed the following general attack stages and features. This is possibly indicative of the attacks originating from the same threat actor(s) or from a widely sold batch with a particular configuration to a variety of actors.
Initial Access
Although Hive actors are known to gain initial access to networks through multiple different vectors, the two primary methods reported by security researchers are the exploitation of Microsoft Exchange vulnerabilities, or the distribution of phishing emails with malicious attachments [2][3].
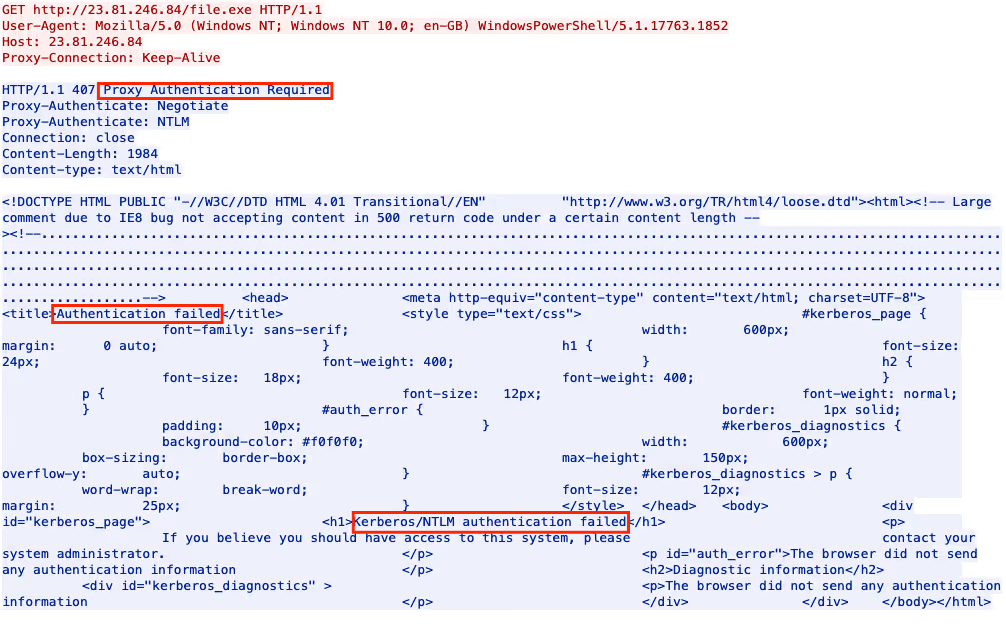
In the early stages of one Hive ransomware attack observed on the network of a Darktrace customer, for example, Darktrace detected a device connecting to the rare external location 23.81.246[.]84, with a PowerShell user agent via HTTP. During this connection, the device attempted to download an executable file named “file.exe”. It is possible that the file was initially accessed and delivered via a phishing email; however, as Darktrace/Email was not enabled at the time of the attack, this was outside of Darktrace’s purview. Fortunately, the connection failed the proxy authentication was thus blocked as seen in the packet capture (PCAP) in Figure 2.
Shortly after this attempted download, the same device started to receive a high volume of incoming SSL connections from a rare external endpoint, namely 146.70.87[.]132. Darktrace logged that this endpoint was using an SSL certificate signed by Go Daddy CA, an easily obtainable and accessible SSL certificate, and that the increase in incoming SSL connections from this endpoint was unusual behavior for this device.
It is likely that this highly anomalous activity detected by Darktrace indicates when the ransomware attack began, likely initial payload download.
Darktrace DETECT models:
- Anomalous Connection / Powershell to Rare External
- Anomalous Server Activity / New Internet Facing System
C2 Beaconing
Following the successful initial access, Hive actors begin to establish their C2 infrastructure on infected networks through numerous connections to C2 servers, and the download of additional stagers.
On customer networks infected by Hive ransomware, Darktrace identified devices initiating a high volume of connections to multiple rare endpoints. This very likely represented C2 beaconing to the attacker’s infrastructure. In one particular example, further open-source intelligence (OSINT) investigation revealed that these endpoints were associated with Cobalt Strike.
Darktrace DETECT models:
- Anomalous Connection / Multiple Connections to New External TCP
- Anomalous Server Activity / Anomalous External Activity from Critical Network Device
- Compromise / High Volume of Connections with Beacon Score
- Compromise / Sustained SSL or HTTP Increase
- Compromise / Suspicious HTTP Beacons to Dotted Quad
- Compromise / SSL or HTTP Beacon
- Device / Lateral Movement and C2 Activity
Internal Reconnaissance, Lateral Movement and Privilege Escalation
After C2 infrastructure has been established, Hive actors typically begin to uninstall antivirus products in an attempt to remain undetected on the network [3]. They also perform internal reconnaissance to look for vulnerabilities and open channels and attempt to move laterally throughout the network.
Amid the C2 connections, Darktrace was able to detect network scanning activity associated with the attack when a device on one customer network was observed initiating an unusually high volume of connections to other internal devices. A critical network device was also seen writing an executable file “mimikatz.exe” via SMB which appears to be the Mimikatz attack tool commonly used for credential harvesting.
There were also several detections of lateral movement attempts via RDP and DCE-RPC where the attackers successfully authenticated using an “Administrator” credential. In one instance, a device was also observed performing ITaskScheduler activity. This service is used to remotely control tasks running on machines and is commonly observed as part of malicious lateral movement activity. Darktrace DETECT understood that the above activity represented a deviation from the devices’ normal pattern of behavior and the following models were breached:
Darktrace DETECT models:
- Anomalous Connection / Anomalous DRSGetNCChanges Operation
- Anomalous Connection / New or Uncommon Service Control
- Anomalous Connection / Unusual Admin RDP Session
- Anomalous Connection / Unusual SMB Version 1 Connectivity
- Compliance / SMB Drive Write
- Device / Anomalous ITaskScheduler Activity
- Device / Attack and Recon Tools
- Device / Attack and Recon Tools In SMB
- Device / EXE Files Distributed to Multiple Devices
- Device / Suspicious Network Scan Activity
- Device / Increase in New RPC Services
- User / New Admin Credentials on Server
Data Exfiltration
At this stage of the attack, Hive actors have been known to carry out data exfiltration activity on infected networks using a variety of different methods. The Cybersecurity & Infrastructure Security Agency (CISA) reported that “Hive actors exfiltrate data likely using a combination of Rclone and the cloud storage service Mega[.]nz” [4]. Darktrace DETECT identified an example of this when a device on one customer network was observed making HTTP connections to endpoints related to Mega, including “w.apa.mega.co[.]nz”, with the user agent “rclone/v1.57.0” with at least 3 GiB of data being transferred externally (Figure 3). The same device was also observed transferring at least 3.6 GiB of data via SSL to the rare external IP, 158.51.85[.]157.

In another case, a device was observed uploading over 16 GiB of data to a rare external endpoint 93.115.27[.]71 over SSH. The endpoint in question was seen in earlier beaconing activity suggesting that this was likely an exfiltration event.
However, Hive ransomware, like any other RaaS kit, can differ greatly in its techniques and features, and it is important to note that data exfiltration may not always be present in a Hive ransomware attack. In one incident detected by Darktrace, there were no signs of any data leaving the customer environment, indicating data exfiltration was not part of the Hive actor’s objectives.
Darktrace DETECT models:
- Anomalous Connection / Data Sent to Rare Domain
- Anomalous Connection / Lots of New Connections
- Anomalous Connection / Multiple HTTP POSTs to Rare Hostname
- Anomalous Connection / Suspicious Self-Signed SSL
- Anomalous Connection / Uncommon 1 GiB Outbound
- Device / New User Agent and New IP
- Unusual Activity / Unusual External Data to New Endpoints
- Unusual Activity / Unusual External Data Transfer
- Unusual Activity / Enhanced Unusual External Data Transfer
Ransomware Deployment
In the final stage of a typical Hive ransomware attack, the ransomware payload is deployed and begins to encrypt files on infected devices. On one customer network, Darktrace detected several devices connecting to domain controllers (DC) to read a file named “xxx.exe”. Several sources have linked this file name with the Hive ransomware payload [5].
In another example, Darktrace DETECT observed multiple devices downloading the executable files “nua64.exe” and “nua64.dll” from a rare external location, 194.156.90[.]25. OSINT investigation revealed that the files are associated with Hive ransomware.

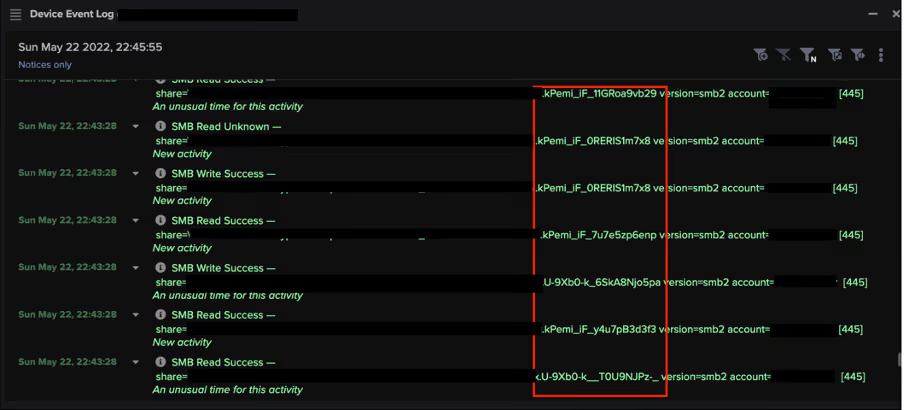
Shortly after the download of this executable, multiple devices were observed performing an unusual amount of file encryption, appending randomly generated strings of characters to file extensions.
Although it has been reported that earlier versions of Hive ransomware encrypted files with a “.hive” extension [7], Darktrace observed across multiple customers that encrypted files had extensions that were partially-randomized, but consistently 20 characters long, matching the regular expression “[a-zA-Z0-9\-\_]{8}[\-\_]{1}[A-Za-z0-9\-\_]{11}”.
Following the successful encryption of files, Hive proceeds to drop a ransom note, named “HOW_TO_DECRYPT.txt”, into each affected directory. Typically, the ransom note will contain a link to Hive’s “sales department” and, in the event that exfiltration took place, a link to the “HiveLeaks” site, where attackers threaten to publish exfiltrated data if their demands are not met (Figure 6). In cases of Hive ransomware detected by Darktrace, multiple devices were observed attempting to contact “HiveLeaks” TOR domains, suggesting that endpoint users had followed links provided to them in ransom notes.

Examples of file extensions:
- 36C-AT9-_wm82GvBoCPC
- 36C-AT9--y6Z1G-RFHDT
- 36C-AT9-_x2x7FctFJ_q
- 36C-AT9-_zK16HRC3QiL
- 8KAIgoDP-wkQ5gnYGhrd
- kPemi_iF_11GRoa9vb29
- kPemi_iF_0RERIS1m7x8
- kPemi_iF_7u7e5zp6enp
- kPemi_iF_y4u7pB3d3f3
- U-9Xb0-k__T0U9NJPz-_
- U-9Xb0-k_6SkA8Njo5pa
- zm4RoSR1_5HMd_r4a5a9
Darktrace DETECT models:
- Anomalous Connection / SMB Enumeration
- Anomalous Connection / Sustained MIME Type Conversion
- Anomalous Connection / Unusual Admin SMB Session
- Anomalous File / Internal / Additional Extension Appended to SMB File
- Compliance / SMB Drive Write
- Compromise / Ransomware / Suspicious SMB Activity
- Compromise / Ransomware / Ransom or Offensive Words Written to SMB
- Compromise / Ransomware / Possible Ransom Note Write
- Compromise / High Priority Tor2Web
- Compromise / Tor2Web
- Device / EXE Files Distributed to Multiple Devices
Conclusion
As Hive ransomware attacks are carried out by different affiliates using varying deployment kits, the tactics employed tend to vary and new IoCs are regularly identified. Furthermore, in 2022 a new variant of Hive was written using the Rust programming language. This represented a major upgrade to Hive, improving its defense evasion techniques and making it even harder to detect [8].
Hive is just one of many RaaS offerings currently on the market, and this market is only expected to grow in usage and diversity of presentations. As ransomware becomes more accessible and easier to deploy it is essential for organizations to adopt efficient security measures to identify ransomware at the earliest possible stage.
Darktrace DETECT’s Self-Learning AI understands customer networks and learns the expected patterns of behavior across an organization’s digital estate. Using its anomaly-based detection Darktrace is able to identify emerging threats through the detection of unusual or unexpected behavior, without relying on rules and signatures, or known IoCs.
Credit to: Emily Megan Lim, Cyber Analyst, Hyeongyung Yeom, Senior Cyber Analyst & Analyst Team Lead.
Appendices
MITRE AT&CK Mapping
Reconnaissance
T1595.001 – Scanning IP Blocks
T1595.002 – Vulnerability Scanning
Resource Development
T1583.006 – Web Services
Initial Access
T1078 – Valid Accounts
T1190 – Exploit Public-Facing Application
T1200 – Hardware Additions
Execution
T1053.005 – Scheduled Task
T1059.001 – PowerShell
Persistence/Privilege Escalation
T1053.005 – Scheduled Task
T1078 – Valid Accounts
Defense Evasion
T1078 – Valid Accounts
T1207 – Rogue Domain Controller
T1550.002 – Pass the Hash
Discovery
T1018 – Remote System Discovery
T1046 – Network Service Discovery
T1083 – File and Directory Discovery
T1135 – Network Share Discovery
Lateral Movement
T1021.001 – Remote Desktop Protocol
T1021.002 – SMB/Windows Admin Shares
T1021.003 – Distributed Component Object Model
T1080 – Taint Shared Content
T1210 – Exploitation of Remote Services
T1550.002 – Pass the Hash
T1570 – Lateral Tool Transfer
Collection
T1185 – Man in the Browser
Command and Control
T1001 – Data Obfuscation
T1071 – Application Layer Protocol
T1071.001 – Web Protocols
T1090.003 – Multi-hop proxy
T1095 – Non-Application Layer Protocol
T1102.003 – One-Way Communication
T1571 – Non-Standard Port
Exfiltration
T1041 – Exfiltration Over C2 Channel
T1567.002 – Exfiltration to Cloud Storage
Impact
T1486 – Data Encrypted for Impact
T1489 – Service Stop
List of IoCs
23.81.246[.]84 - IP Address - Likely Malicious File Download Endpoint
146.70.87[.]132 - IP Address - Possible Ransomware Endpoint
5.199.162[.]220 - IP Address - C2 Endpoint
23.227.178[.]65 - IP Address - C2 Endpoint
46.166.161[.]68 - IP Address - C2 Endpoint
46.166.161[.]93 - IP Address - C2 Endpoint
93.115.25[.]139 - IP Address - C2 Endpoint
185.150.1117[.]189 - IP Address - C2 Endpoint
192.53.123[.]202 - IP Address - C2 Endpoint
209.133.223[.]164 - IP Address - Likely C2 Endpoint
cltrixworkspace1[.]com - Domain - C2 Endpoint
vpnupdaters[.]com - Domain - C2 Endpoint
93.115.27[.]71 - IP Address - Possible Exfiltration Endpoint
158.51.85[.]157 - IP Address - Possible Exfiltration Endpoint
w.api.mega.co[.]nz - Domain - Possible Exfiltration Endpoint
*.userstorage.mega.co[.]nz - Domain - Possible Exfiltration Endpoint
741cc67d2e75b6048e96db9d9e2e78bb9a327e87 - SHA1 Hash - Hive Ransomware File
2f9da37641b204ef2645661df9f075005e2295a5 - SHA1 Hash - Likely Hive Ransomware File
hiveleakdbtnp76ulyhi52eag6c6tyc3xw7ez7iqy6wc34gd2nekazyd[.]onion - TOR Domain - Likely Hive Endpoint
References
[1] https://www.justice.gov/opa/pr/us-department-justice-disrupts-hive-ransomware-variant
[2] https://www.varonis.com/blog/hive-ransomware-analysis
[3] https://www.trendmicro.com/vinfo/us/security/news/ransomware-spotlight/ransomware-spotlight-hive
[4]https://www.cisa.gov/news-events/cybersecurity-advisories/aa22-321a
[5] https://www.trendmicro.com/en_us/research/22/c/nokoyawa-ransomware-possibly-related-to-hive-.html
[6] https://www.virustotal.com/gui/file/60f6a63e366e6729e97949622abd9de6d7988bba66f85a4ac8a52f99d3cb4764/detection
[7] https://heimdalsecurity.com/blog/what-is-hive-ransomware/
[8] https://www.microsoft.com/en-us/security/blog/2022/07/05/hive-ransomware-gets-upgrades-in-rust/




























%201.png)










